Directory
Directory shows an overview of your environment with metrics in a series of cards with the number of identities, groups, devices, and apps that ITDR is monitoring within your environment. Click a card to see more information.
Identities
The Identities view shows a list of identities that have been captured from your identity provider. The following information about users appears above the full card or list view:
- Identities Not Protected by MFA: A count of users that don't have multi-factor authentication (MFA) configured on their account.
- Dormant Accounts: A count of users that haven't signed in within the last 90 days.
- Admin Accounts: A count of users that have an admin role within the Microsoft Entra ID tenant.
Identity icons and tags
Identities have different icons and sets of tags to help you quickly identify the type of account and its associated attributes. These appear in the card view, in the Risky Users widget, and within the Identity Details page. Identities may have the following icons and tags.
The following additional tags based on attributes related to the account as well as analysis and processing by the system may also show:
- Admin tag: The account has been identified as an admin in the identity provider.
- Guest tag: The account is a guest in your tenant.
- Deleted User tag: The account has been deleted from your tenant.
- Locked User tag: The account has been disabled.
- MFA User tag: The account has MFA enabled.
- Compromised tag: The account has an active credential leak.
- Dormant Account tag: The account hasn't signed in within the last 90 days.
- Cloud Only tag: The account doesn't have on-premise identifiers, indicating it's only present in the cloud identity provider.
- Hybrid tag: The account contains on-premise identifiers, indicating it's being synced and can access both cloud and on-premise resources.
- Human tag: The account is associated to a human user.
- VIP tag: The account is configured for VIP monitoring. For details, see Select users for VIP monitoring.
Adjust Identities View
Adjust the Identities view using the following controls:
- Switch between card view or list view using the icons above the table.
- By default, users are sorted alphabetically by name. Change the sort order using the drop-down menu above the table.
- Filter the identities by name using the Search Identities field.
-
Filter the identities by the following attributes:
- Status: The status of the identity within the identity provider.
- Department: The department of the user, if defined within the identity provider.
- Employee Type: The type of employee, if defined within the identity provider.
- Is Admin: Whether the user has the admin flag set within the identity provider.
- Is Guest: Whether the user is a guest within the identity provider.
- Is Dormant: Whether the user is considered dormant due to having not signed in within the last 90 days.
- Has MFA: Whether the user has MFA configured on their account within the identity provider.
- Has Passwordless MFA: Whether the user has a stronger MFA method defined, such as passwordless MFA.
- Country: The user's country, if defined within the identity provider.
- Region: The user's region, if defined within the identity provider.
- MFA Method: Shows users filtered by the selected MFA method, if applicable.
- Is Compromised: Shows users filtered by whether they have active credential leaks.
- Is Cloud Only: Shows users filtered by whether they're only registered in the cloud.
Note
Some filters may lack data if it's not available from the identity provider.
Adjust card view
When viewing users in card view, click the down arrow at the bottom of a card to expand the card to view more details. Only one card can be expanded at a time.
Adjust list view
When viewing users in list view, take the following actions:
- Click the arrow at the left of a row to expand the row to view more details.
- Click the menu icon of any column to pin, auto-size, reset, and add or remove columns.
View identity details
Click the Display Name at the top of a card in card view or from the list view table to go to the Identity Details page. For more information, see Identity Details.
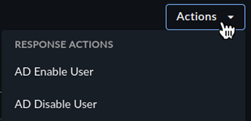
Take response actions
If you opted to authorize response actions, you can run these actions on a user. Click the Actions menu from an expanded card in card view or the Actions column in list view, and choose the desired response action.
Groups
The Groups view shows a list of groups that have been captured from your identity provider. Search groups using the search field above the table, or use the following filters:
- Deleted: Whether the group is deleted within the identity provider.
- Mail Enabled: Whether email can be sent to the group.
- Security Enabled: Whether the group can be used to control user access to resources.
- Assignable to Roles: Whether the group is assignable to roles.
For more information on Microsoft Entra ID groups, see Security groups and mail-enabled security groups.
Group Details
Click a Group Name to open a dedicated details page with retrieved group metadata and a table of identities associated with the group.
Devices
The Devices view shows a list of devices that have been registered within your Microsoft Entra ID tenant. Devices include both personal or company-owned devices that users can access company resources from. For more information, see Microsoft Entra registered devices.
Search devices using the search field above the table, or use one of the following filters:
- State: The state of the device as reported by the identity provider, such as active or disabled.
- Ownership: The ownership of the device as reported by the identity provider, such as personal, company, or unknown.
- Operating System: The operating system as reported by the identity provider.
- Architecture: The device architecture as reported by the identity provider.
- Manufacturer: The device manufacturer as reported by the identity provider.
- Model: The device model as reported by the identity provider.
- Rooted: Whether the device is reported by the identity provider to have been rooted.
- Managed: Whether the device is considered managed by the identity provider.
- Compliant: Whether the device is considered compliant by the identity provider.
Availability of details for a device is subject to what is provided by the identity provider. For details about Microsoft Entra ID devices, see What is a device identity?.
Device Details
Click a Display Name to open a dedicated details page listing retrieved device metadata, associated identities, related findings, and more, depending on the type of device.
Apps
The Apps view shows a list of the enterprise applications registered within your Microsoft Entra ID tenant. Enterprise applications are a type of service principal, or non-human identity, that is the local representation, or application instance, of a global application object in a single tenant or directory. In this case, a service principal is a concrete instance created from the application object and inherits certain properties from that application object. A service principal is created in each tenant where the application is used and references the globally unique app object. The service principal object defines what the app can actually do in the specific tenant, who can access the app, and what resources the app can access.
For more information about Entra ID and their service principal objects, see Application and service principal objects in Microsoft Entra ID.
App Details
Click a Display Name to open a dedicated details page listing retrieved metadata, related findings, and app owners.