Identity Risk Posture
Identity Risk Posture provides an overview of your current identity posture, including your current score and rating, as well as the number of identities, groups, devices, and applications, or service principals, we're monitoring. In addition, you can view the top risky users, top findings, and credential leak metrics.
Identity Risk Posture score and rating
The Identity Risk Posture score and rating use a weighted average based on the number of open findings and the risk level of those findings identified within your environment. Critical- and high-risk findings are weighted higher than medium- and low-risk findings. The score is updated daily and increases or decreases based on whether findings are remediated or dismissed, or new findings are discovered. In addition, you can see how the score changed from the previous day by the percent change and arrow.
The following are possible ratings and associated scores:
- Critical: 75-100
- High: 50-74
- Medium: 25-49
- Low: 0-24
Click the Identity Risk Posture score to open the Risk Posture Score details. For more information, see Risk Posture Score.
Your environment statistics
Next to the score and rating, find counts of identities, groups, devices, and applications we're monitoring from your Entra ID environment. Click one of these counts to go to the associated section of the Directory page. For more information, see Directory.
Top Risky Users widget
The Top Risky Users widget shows a list of users that have been involved in detections within the last seven days. For each user, a count of both open and closed detections for each severity is included.
Take the following actions from this widget:
- Click the user's name or icon to go to the Identity Details page for that user. For more information, see Identity Details.
- Click the detection counts for a user to go to the Insights tab of the related Identity Details page.
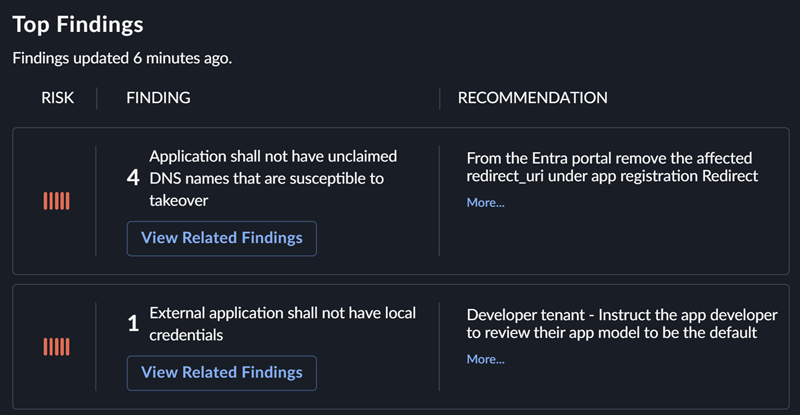
Top Findings widget
The Top Findings widget displays the top ten findings sorted by risk, combining multiple instances of the same finding with an occurrence count. Take the following actions from this widget:
- Click More from a recommendation to expand the row and view the full recommendation. Click Less to collapse the row again.
- Click View Related Findings to go to the Identity Findings page, which is filtered by the check that identified the issue.
- Click View All Findings from the bottom of the widget to go to the Identity Findings page.
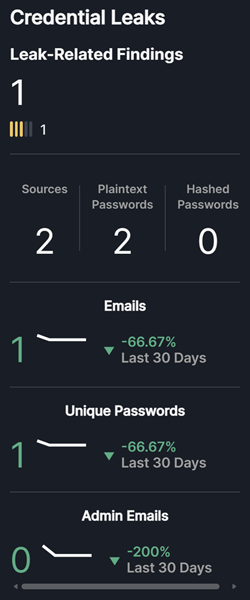
Credential Leaks widget
The Credential Leaks widget shows the count of open leak-related findings sorted by risk level, as well as metrics related to leaked credentials found for the domains configured within your environment. Where applicable, it also shows the trend of this activity over the last 30 days.
The statistics in the widget include all known active credential leaks. This could include data for users who are no longer with the organization or old leaked data matching the selected domains. We only generate findings for what we consider active leaks that include an active matching identity, so the following statistics may differ from what you see within the Findings view.
- Leak-Related Findings: The number of open credential leak findings with counts by risk level.
- Sources: The number of active unique leak sources where data for your domains has been observed.
- Plaintext Passwords: The number of active leaks where plaintext passwords were found in the leak data.
- Hashed Passwords: The number of active leaks where hashed passwords were found in the leak data.
- Emails: The number of active unique email accounts that have been observed in the leak data.
- Unique Passwords: The number of active unique passwords that have been observed in the leak data.
- Admin Emails: The number of active accounts identified as an admin that have been observed in the leak data.
Take the following actions from this widget:
- Click Leak-Related Findings to go to the Identity Findings page filtered by dark web intelligence findings. For more information, see Findings.
- Click a metric to view matching leak data on the Dark Web Intelligence page. For more information, see Dark Web Intelligence.