Endpoint
You install an Endpoint agent on workstations to protect them against malware, risky file types and websites, and malicious network traffic.
It also offers peripheral control, web control and more.
Sophos Device Encryption is also installed automatically on Windows computers (if you have the required license).
Note
On Windows computers, we create some user groups that are used by Sophos Anti-Virus. These groups are SophosUser, SophosPowerUser and Sophos Administrator. Don't delete them.
For help with setting up your firewall or proxy to communicate between Sophos Central Admin and your managed endpoints, see Domains and ports to allow.
Download and run installers
Some options may not be available for all customers yet.
You need to download an installer and run it on computers. You can choose from two sets of installers:
- Installers for Protection, ZTNA, and Encryption
- Installers for XDR Sensor
Note
Endpoint installers are for Windows and macOS only. For Linux installers, look under Server.
Protection, ZTNA, and Encryption
- Go to My Environment > Installers.
-
In Endpoint, do one of the following:
- Click Download Complete Windows Installer or Download Complete macOS Installer. These installers include all endpoint products your license covers.
-
Click Choose Components to choose which products will be included in the installer.
If you select XDR Sensor, we won't install protection. You must have third-party protection installed.
-
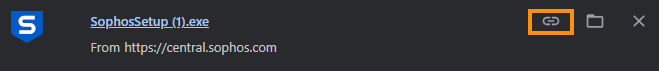
Go to the Downloads folder and run the installer.
You can go to your browser's download history to copy the download link and send it directly to your users. They can use the download link to download the installer.
Alternatively, click Send Installers to Users. For more information, see the section below.
Send installers to users
Send a personalized email with deployment instructions to selected users. The device will be automatically associated with the user in Sophos Central when deployed.
To send installers to users, do as follows:
- Go to My Environment > Installers.
- In Endpoint, click Send Installers to Users.
- On the Users & Groups page, select the users for which you want to send the installer link.
- Click Email Setup Link.
-
In Email Setup Link, do as follows:
- In Deployment Emails, under Endpoint, select Computers.
- Click Save.
The selected users will receive an email from do-not-reply@central.sophos.com. They must click the relevant link to download the installer for their operating system. They can then go to their Downloads folder and run the installer.
XDR Sensor installers
XDR Sensor detects threats and works alongside third-party protection.
XDR Sensor doesn't protect against threats. You must have third-party protection installed. You must also have a licence that includes XDR.
- Go to My Environment > Installers.
- In Endpoint, under XDR Sensor Installers, click the installer for your operating system.
- Go to the Downloads folder and run the installer.
Deployment tools
You must download the macOS configuration profiles before you download your installer. For more information, see Download the macOS configuration profiles.
Before you install on macOS
Find out what you need to know before you install our protection software on macOS.
- You must move the
SophosInstall.zipfile to a location that's not in the user’s Documents, Desktop, or Downloads folders. We recommend the user's home folder. -
After the
.zipfile is extracted, check if the Apple quarantine flag is set correctly. Do as follows:- Run
xattr ~/SophosInstall/Sophos\ Installer.app. This command will likely displaycom.apple.quarantine. - If the attribute
com.apple.quarantineis present, runsudo xattr -r -d com.apple.quarantine ~/SophosInstall/Sophos\ Installer.app. - Run the installer normally.
If the files are extracted in a different location, adjust the paths accordingly.
Tip
You can use
~as a shortcut for the user's home folder instead of/Users/username. - Run
What happens when you protect a computer
When you protect a computer:
- Each user who logs in is added to the users list in Sophos Central automatically.
- Default policies are applied to each user.
- Each computer is added to the Computers list in Sophos Central.
How we handle Windows usernames and login names
Users are listed with full login name, including the domain if available (for example, DOMAINNAME\jdoe).
If there is no domain, and a user logs in to multiple computers, multiple user entries are displayed for this user, for example MACHINE1\user1 and MACHINE2\user1. To merge these entries, delete one and assign the login to the other (and rename the user, if required). See Endpoint agent mode deployment methods.