Sophos Mailflow Tamper
If any configuration changes from M365 console could impact Sophos Mailflow setup, you will be notified.
Sophos creates transport rules and connectors in M365 to route messages from Microsoft 365 to Sophos Mailflow and back to Microsoft 365. If these rules or connectors are changed directly from M365 console, it could impact the functioning of Sophos Email for the domain.
Sophos Email monitors these changes made in M365 configuration and notifies the admin if any of these changes could tamper Sophos Mailflow setup. This includes, but is not limited to, disablement, deletion, or modification of a connector or a transport rule necessary for MFR.
Note
Sophos Email can monitor these changes in M365 only if auditing is turned on in M365 and Sophos has the necessary permissions. Please follow the steps mentioned below to achieve these two.
-
Turn auditing on
The logs will be generated in Microsoft only if the auditing has been turned on in M365. To turn on the auditing in M365, see M365 documentation - Turn auditing on or off.
-
Grant necessary permissions
Sophos Email App must have the permission Read activity data for your organization to read the audit logs generated in Microsoft 365. If you have setup the mailflow for any of your domains before April 12, 2022, you must disconnect and reconnect the domains to grant the additional permission Sophos Email needs. If your mail flow rules are configured on or after April 12, 2022, Sophos should already have this permission.
These alerts are of different severity (High, Medium and Low) which represent the confidence level of the potential impact to Sophos Mailflow.
- A High level alert means a high level of confidence that Sophos Mailflow setup is impacted.
- A Medium level alert means a reasonable level of confidence that the setup is impacted.
- A Low level alert is generally for information purpose only.
You are notified in 3 ways:
-
Alerts in Sophos Central
You can see the alert generated in Centrals global dashboard. The alerts are generated for all severity (High, Medium, and Low).
-
Email notifications
An additional notification email is sent to the Admins and Super-admins of the Sophos Central account. The notification emails are sent only for "High" and "Medium" level alerts.
-
Status Update in Domain Settings page
You can see a changed status of the domain in M365 Domain Settings page. The domain status changes only for "High" and "Medium" severity alerts.
Alerts in Sophos Central
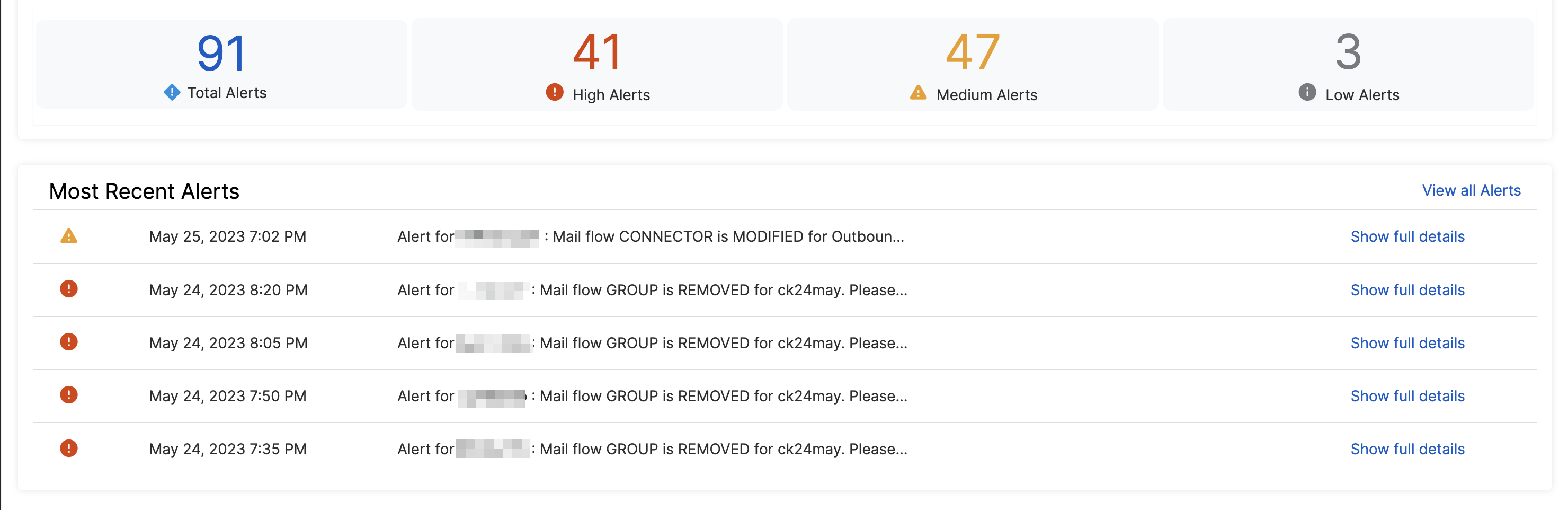
Sophos Central’s global dashboard shows the most recent alerts. If the MFR related alerts are the most recent ones, those will appear here.
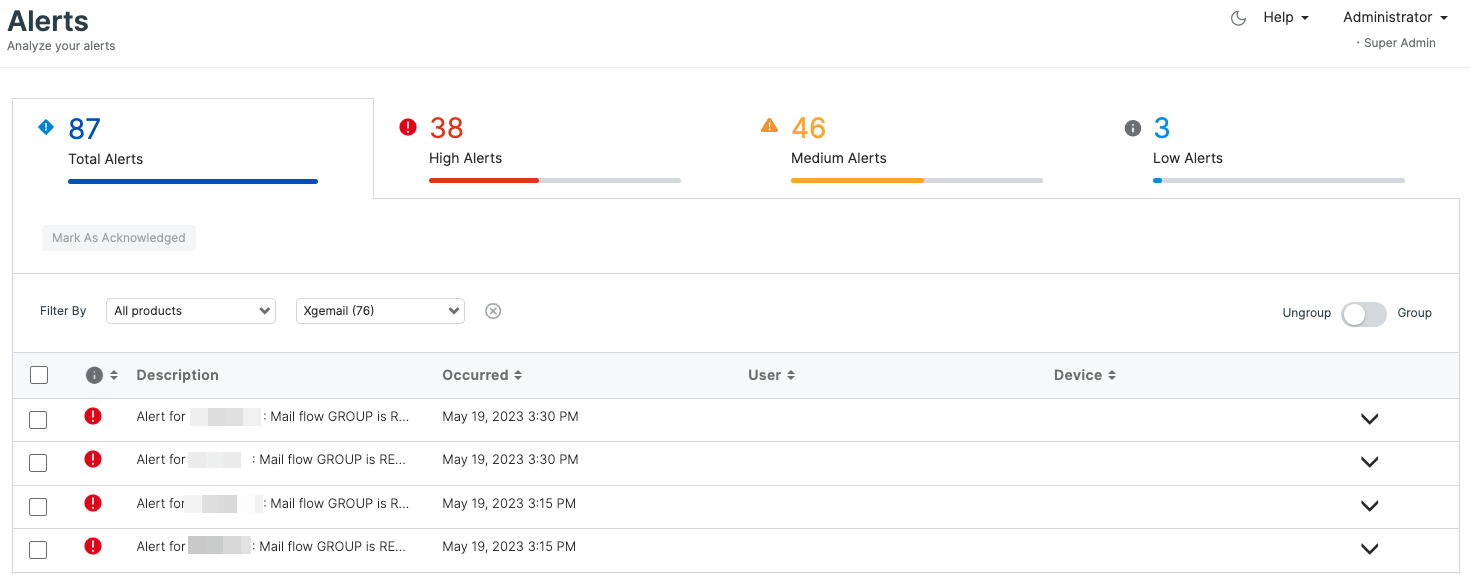
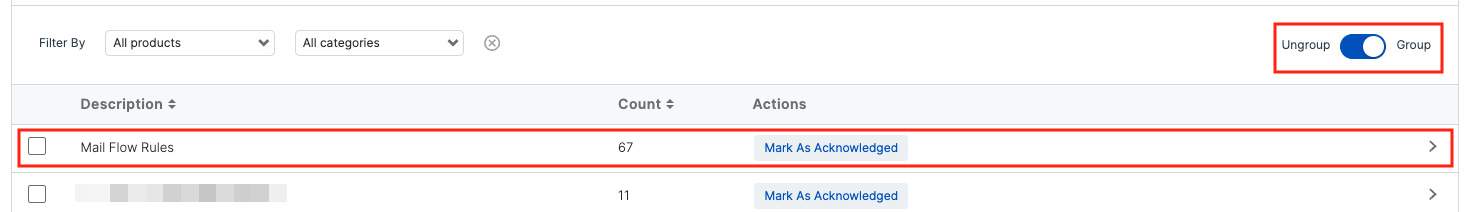
Alternatively, you can go to the Alerts section from left navigation panel to see all the alerts generated. A convenient way to find Mail Flow Rules related alerts is to turn on Group and click on the row with description as Mail Flow Rules.
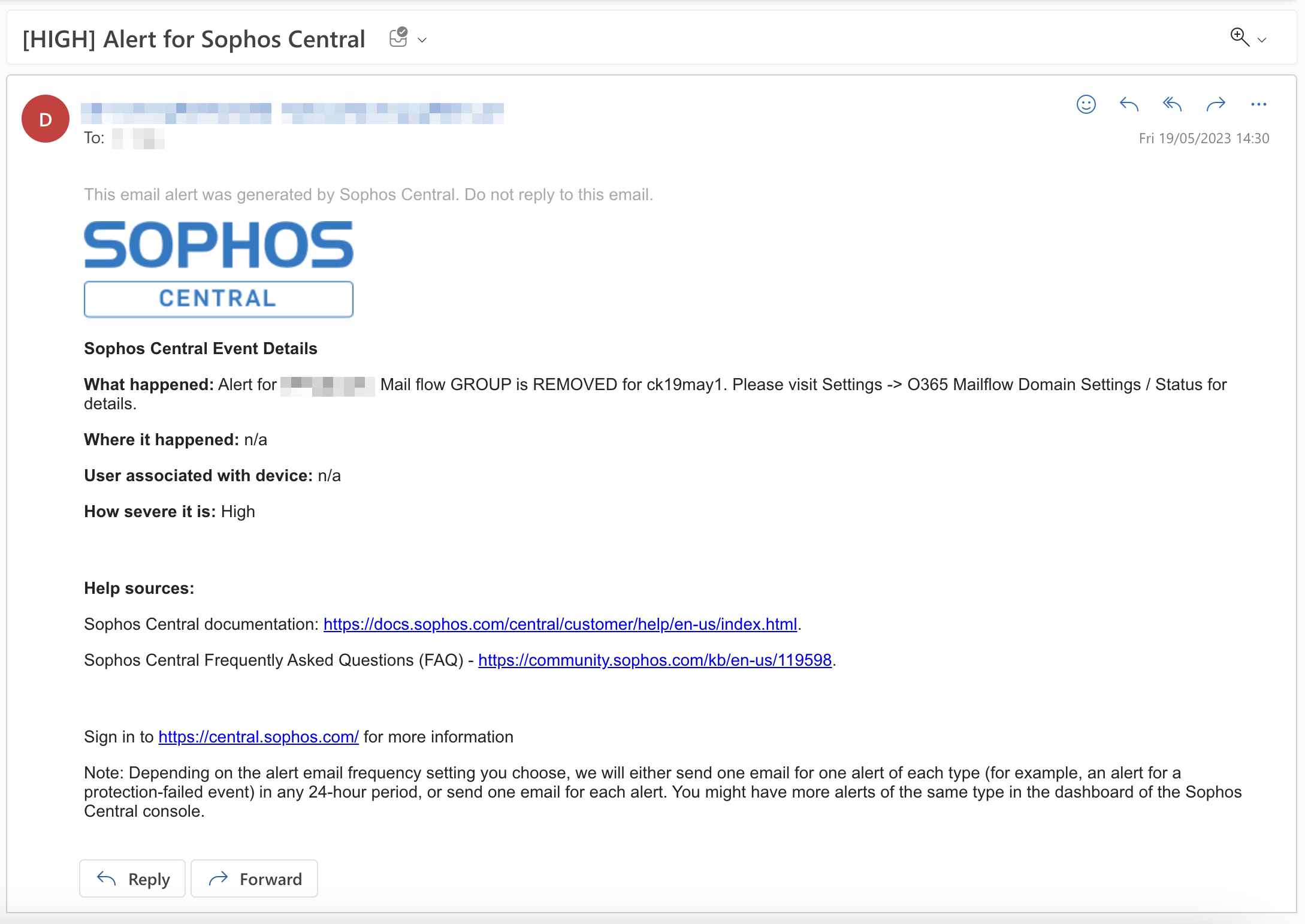
Email Notification
The email notification is generated for "High" and "Medium" severity alerts. The email will look like the one below.
Status Update in Domain Settings page
In Sophos Central, click the Global Settings icon ![]() . Go to Products and Services > Email and click M365 Mailflow Domains.
. Go to Products and Services > Email and click M365 Mailflow Domains.
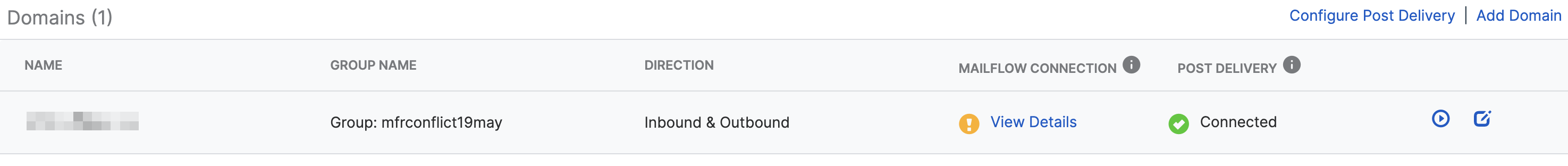
In case an alert is generated, the Mailflow Connection status for the affected domain will change to (!) with an option to View Details.
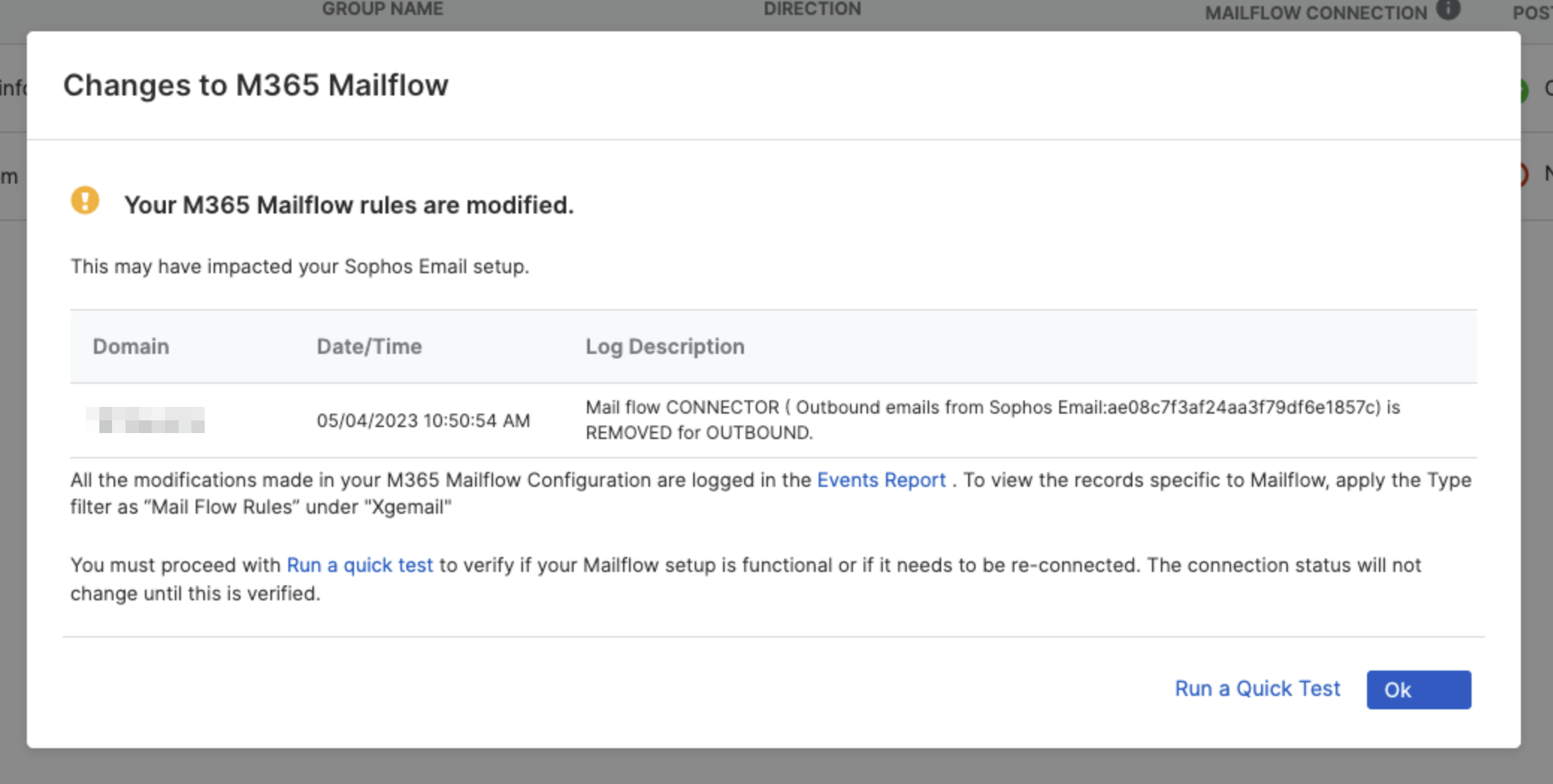
When you click on View Details, you can see the domain name, the date and time of the change made, the name of the rule or connector which was changed, and the exact change that was made.
What to do when you see an alert
If you receive an alert regarding potential domain tampering, it's important to investigate accordingly. Domain tampering occurs when unauthorized changes are made to your domain settings, potentially leading to security vulnerabilities or disruptions in your system.
An alert doesn't necessarily mean that your MFR setup is broken. It's to notify you that some configuration in M365 has changed, and you should review the configuration and make sure the MFR setup is intact.
Warning
Don't remove the configuration of the xgeconnector.com domain. Doing so might break the email flow and stop email processing. If the domain is removed, this will generate a tamper alert.
Every time the domain is added to a tenant, a DNS entry is created within the domain. Since Sophos manages the domain, any DNS changes can only be performed by Sophos. Simply re-adding the domain won't allow you to resolve DNS issues, so you must disconnect and reconnect before making any changes.
If you see an alert, follow the below steps based on your scenario:
-
Alert generated because the group name was changed in M365.
If the alert was generated because you changed the group name (DL name) in Microsoft 365 that you’re using in Sophos Mailflow, do as follows:
- Confirm that the DL name is synchronized in Sophos Central.
- Update the group name in the Sophos Central’s M365 domain settings page. When you save the changes, the MFR setup will be corrected, the status will be back to Connected.
-
All other alerts (known and intentional changes).
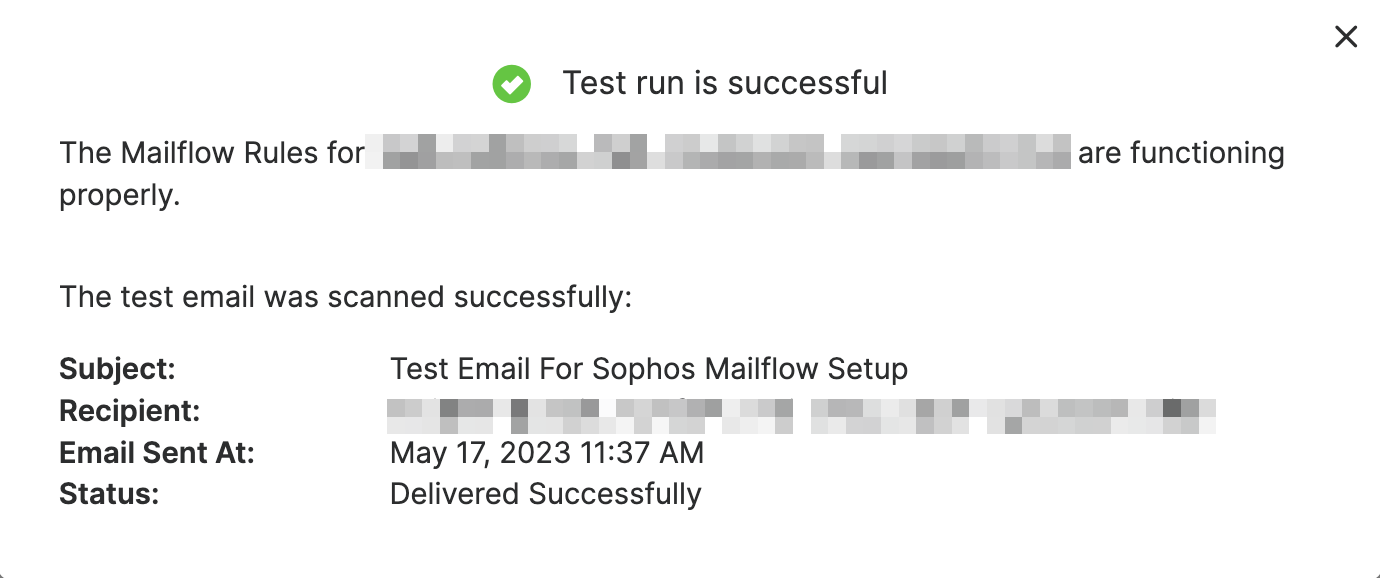
If you recognize the change and you want to keep it, but you are unsure if this has impacted the mail flow setup, use Run a Quick Test.
-
All other alerts (unknown or unintentional changes).
If you do not recognize the change, but you know how to correct/fix it from Microsoft 365 portal, you should make the necessary correction in M365. Once that is done, come back to Sophos Central and use Run a Quick Test.
If you do not know how to correct/fix the issue in M365 portal, you should still go ahead and run a quick test in Sophos Central. If the setup is intact, Run a Quick Test will be successful.
Success
If Run a Quick Test is successful, the (!) sign will go away for the domain, and the status will return to (green tick).
Failure
If the test fails and/or you are not sure how to fix the issue, simply follow the Reconnect flow in Sophos Central M365 domain status page. The reconnection process will ask you for authentication and create (or enable) the missing (or disabled) rules or connectors on the Microsoft side. To start the reconnect flow, hover over View Details and click the green tick that appears.
Tip
If the issue persists, a manual cleanup may be needed. Please contact Sophos support.