Query Protected Browser data using Live Discover
You can query the Protected Browser data using Live Discover in the Threat Analysis Center. Live Discover lets you use SQL queries to get more granular data than the reports in Logs & Reports.
To use Live Discover for Protected Browser, go to Threat Analysis Center > Live Discover and click ZTNA.
You must create new queries to get the Protected Browser data. To create new queries, turn on Designer Mode. For information about how to use Live Discover, see Live Discover.
Note
When you're creating a new query for Protected Browser, select Data Lake as the Source.
Data Lake schema
For information about the tables and data available, you can see the Data Lake schema in the schema viewer.
To open the schema viewer, do as follows:
- Go to Threat Analysis Center > Live Discover and click ZTNA.
- Make sure Designer Mode is turned on.
- In the Query section, click Create new query.
-
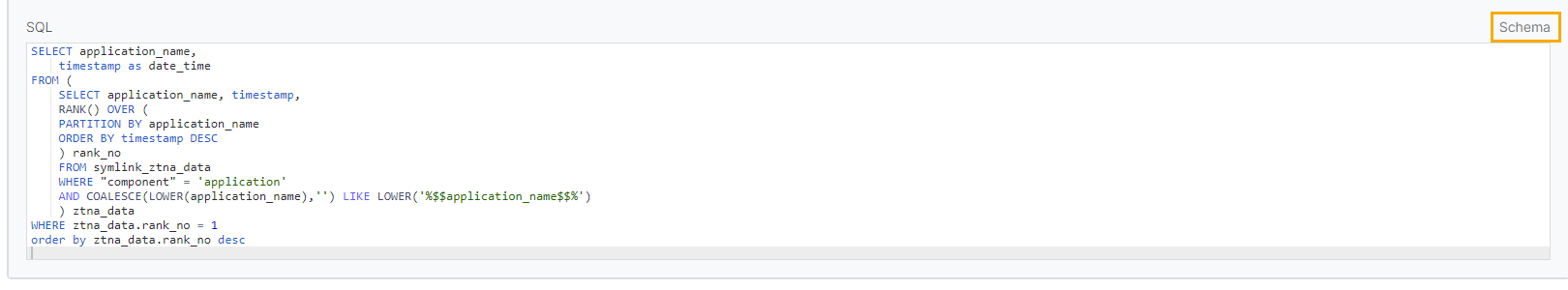
In the upper-right corner of the SQL dialog, click Schema.
The schema viewer opens in a new tab.
-
In the Data Lake drop-down list, select ZTNA.
During the EAP, the Protected Browser field names are included in the ZTNA table.
Protected Browser field names
The following table describes the Protected Browser field names in the Data Lake:
| Field name | Description |
|---|---|
| customer_id | UUID of the customer |
| gateway id | UUID of the gateway |
| timestamp | Timestamp of when the application was accessed |
| component | Protected Browser component |
| gateway_name | Name of the ZTNA gateway used to access the agentless RDP or SSH application |
| user_name | Name of the user who accessed the application |
| application_name | Name of the accessed application |
| operating_system | Operating system of the device that accessed the application |
| browser_version | Protected Browser version |
| sync_sec_health_status | Health status of the endpoint from which the application was accessed, available only if Sophos Intercept X is installed |
| log_type | Log type. Possible values: Navigation, SSH, RDP, Login, or Logout |
| log_subtype | Status of the application access verdict, indicating whether or not the user was allowed to access the application. |
| log_version | Log version |
| user_email | Email address of the user who accessed the application |
| user_full_name | Full name of the user who accessed the application |
| policy_id | ID of the policy applied to the accessed application |
| policy_name | Name of the policy or base policy applied to the accessed application |
| http_category | Name of the SXL web category |
| http_risk_score | Risk score of the accessed URL |
| http_risk_level | Risk level of the accessed URL derived from the risk score |
| url | URL of the accessed application |
| domain | Domain of the accessed application |
| frame_url | URL shown in the address bar |
| src_ip | Private IP address of the user who accessed the application |
| public_src_ip | Public IP address of the user who accessed the application |
| application_category | Category name of the accessed application |
| application_category_id | Category ID of the accessed application |
| zt_used | Whether or not the requested RDP or SSH application was accessed |
| sophos_endpoint_detected | Whether or not Sophos Endpoint protection was detected as part of the device posture policy |
| other_endpoint_detected | Whether or not third-party endpoint protection was detected as part of the device posture policy |
| session_username | Username used to sign in via SSH or RDP |
| user_country | Country from which the application was accessed |
| user_country_code | Country code of the country from which the application was accessed |
| chromium_version | Chromium version running on Protected Browser |
| disk_encryption_enabled | Whether or not disk encryption was enabled on the end user device |