Cases
You must have Sophos EDR, XDR, or MDR to use this feature.
The Cases page groups together suspicious events reported by our Detections feature and helps you or the MDR team investigate them and respond.
How cases work
We create and manage cases for you automatically or you can create and manage your own.
Cases Sophos manages
We create cases for you automatically. These focus on the detections that we think need investigation.
- We create a case when there's a high-risk detection if it hasn't already been included in a case on the same day.
- We add later detections to the case if they share the same detection type.
- If the case is based on MDR detections, we investigate and respond. This is a "Sophos-managed" case.
Note
If the case is based on Sophos XDR detections, we don't investigate. See Cases you manage.
Cases you manage
If we create a case based on XDR detections, it's a "Self-managed" case. When you review your cases, look for "Self" in the "Managed by" details. You must assign the case to an administrator for investigation. See Assign cases.
You can also create and manage your own cases manually. See Create cases.
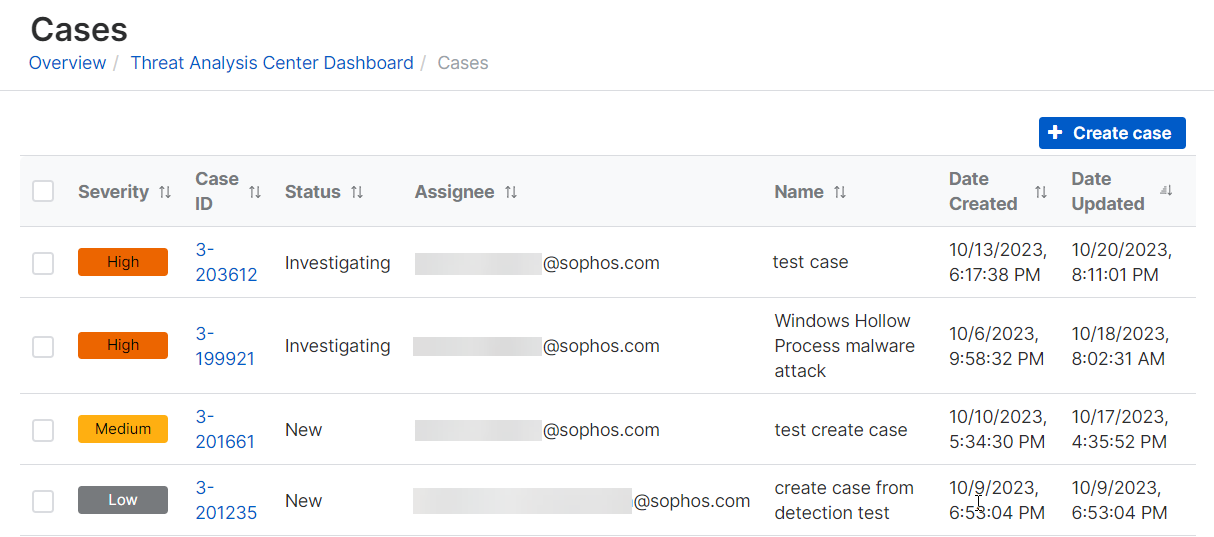
View cases
To view your cases, go to Threat Analysis Center > Cases.
Note
The first time you view this page, the list might be empty. Come back later to see automatically-created cases, or create your own. If you still don't get cases, see Troubleshoot cases.
The Cases list includes the following details for each case.
Severity
| Level | Color | Description |
|---|---|---|
| Critical | Red | A confirmed compromise or unauthorized access to systems. |
| High | Orange | Detections that indicate a targeted attack that could cause a compromise or unauthorized access. |
| Medium | Yellow | Detections that might not be malicious by themselves and aren't known to be targeted. |
| Low | Dark gray | Detections that don’t indicate poor health, malicious activity, or a compromise or unauthorized access. |
| Info | Light gray | A special severity level typically used for initial health checks. |
Status
Sophos-managed cases can show the following statuses:
- Investigating: We're still analyzing the data.
- Action required: You need to take action. We've notified your contacts.
- Resolved: We've resolved the threat.
Self-managed cases let you set the following statuses:
- Investigating: You're still analyzing the data.
- On Hold: You've paused the investigation.
- Resolved: You've resolved the threat.
Note
You can change the status even if the case hasn't been assigned to a specific administrator.
Managed by
You can see who manages the case:
- Sophos: Our MDR team investigate the case and respond. You can’t make any changes but you can reply to the MDR team on the case.
- Self: You must investigate the case and respond.
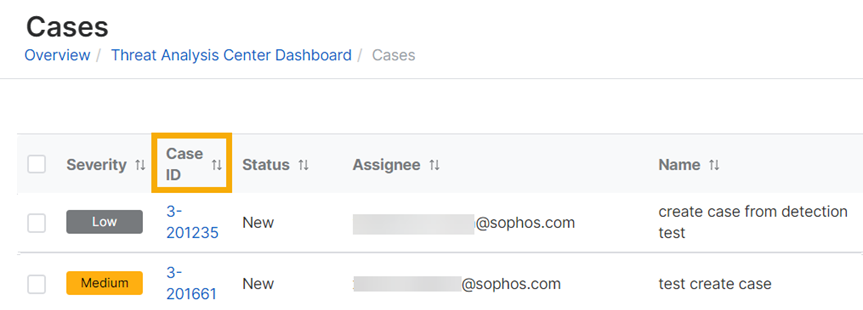
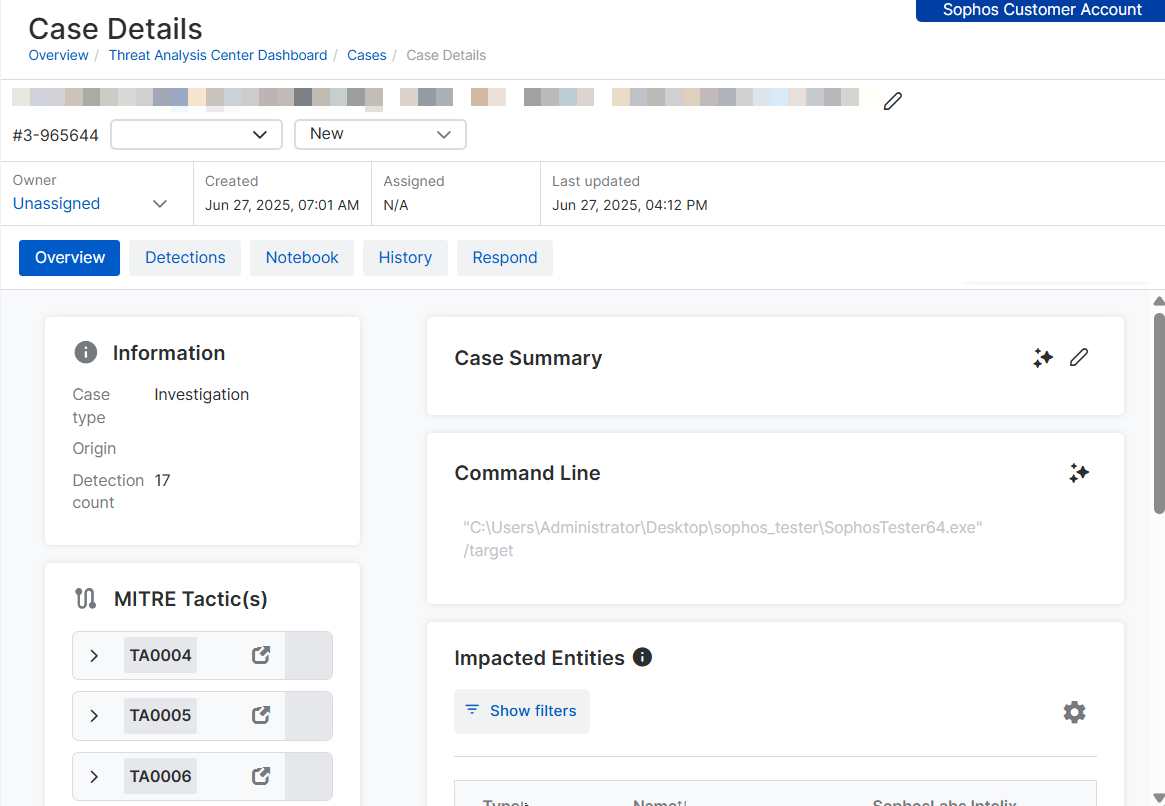
See case details
To see the details of a case and follow its progress, do as follows:
-
On the Cases page, click the Case ID next to the case.
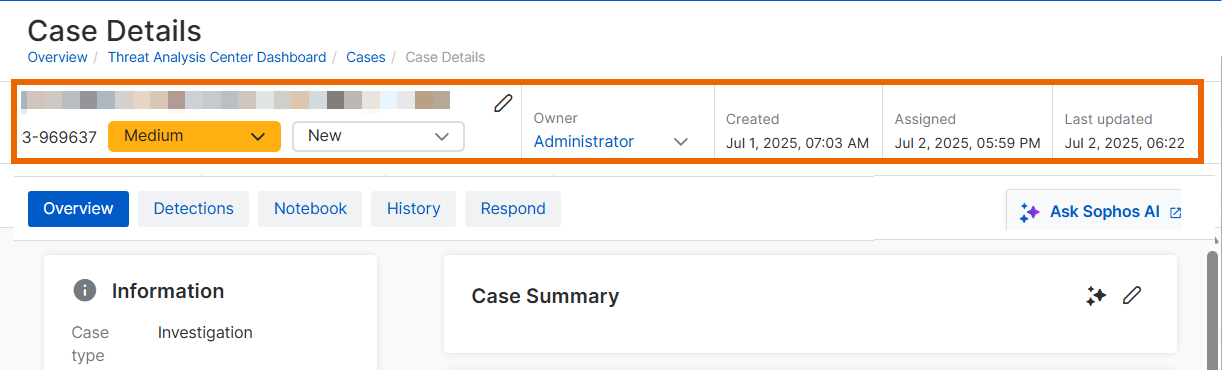
-
On the Case Details page, the page header shows the severity, status, and owner. It also shows when the case was created, assigned, and last updated.
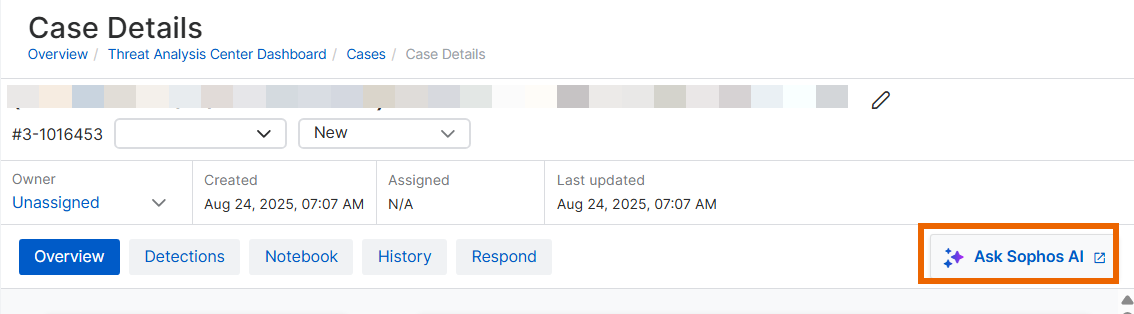
-
If the case is Self-managed, click Ask Sophos AI on the right of the page to use the Sophos AI assistant to investigate the case.
For help with using the assistant, see AI assistant.
The Case Details page also has tabs for further details.
Overview tab
The Overview tab is open by default. It shows how many detections have been added to the case, the MITRE tactics detected, the devices and users affected, a case summary, and details of recent activity on the case.
For Self-managed cases, this tab lets you use AI tools to investigate the case. See Investigate cases.
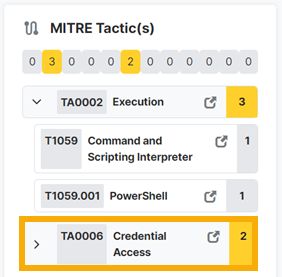
MITRE tactics
MITRE tactics lists any MITRE ATT&CK tactics and techniques we detected.
Click the fold-out arrow beside a tactic to see the technique.
Click the link beside any tactic or technique, for example Credential Access, to go to its details on the MITRE website.
Case summary
If you're an MDR customer, the MDR team enters a case summary for you. If you're an XDR customer, you can use Sophos AI to generate a case summary, or enter your own summary.
Command line
The command line run by the threat that generated the case. If you're an XDR customer, you can use Sophos AI to analyze the command line to discover its intentions and possible impact.
Recent activity
Recent activity shows recent changes to the case. Click See all to go to the History tab.
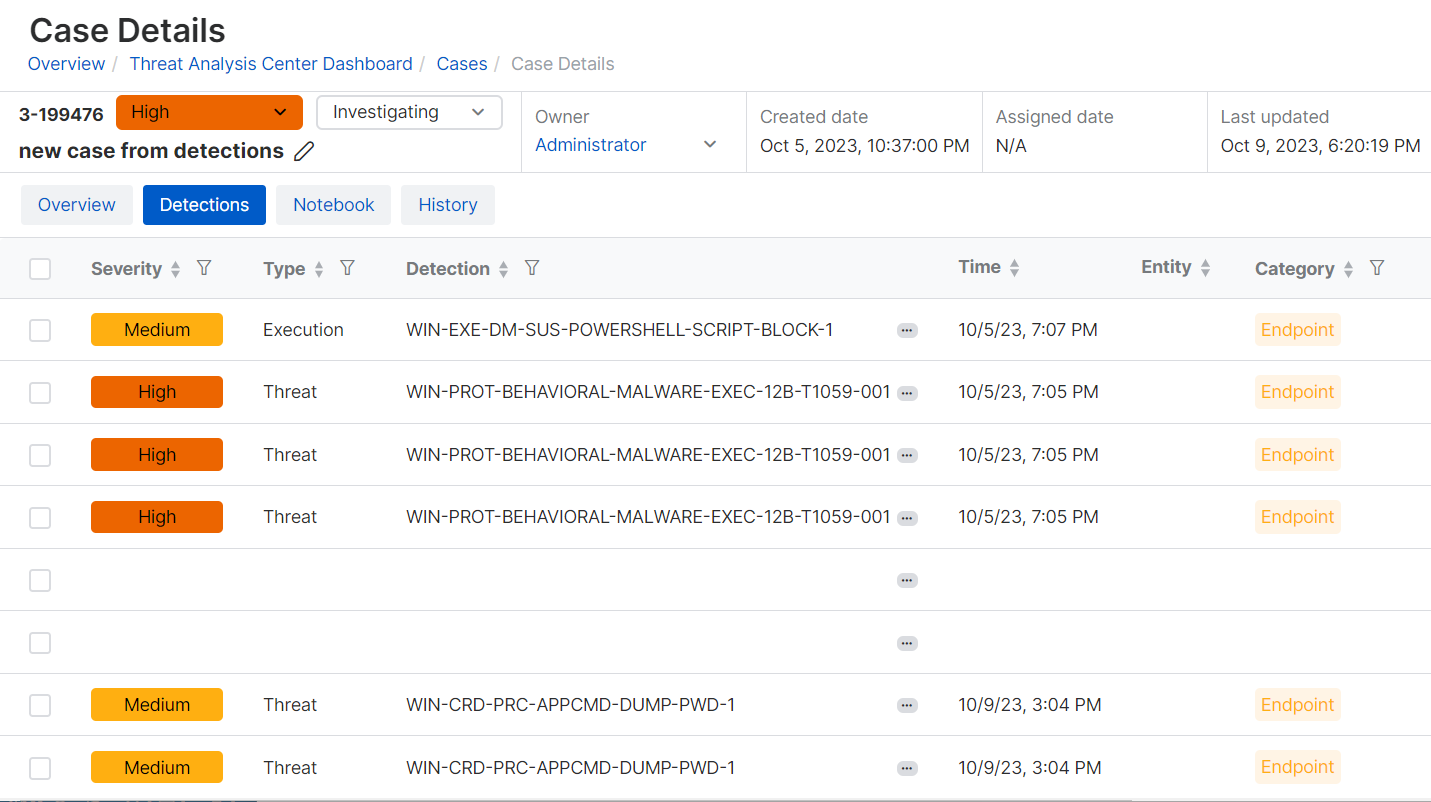
Detections tab
The Detections tab lists all the detections included in the case. It shows the same details as the list on the Detections page. See Detections.
Notebook tab
If you're working on a Self-managed case, use the Notebook tab to keep a record of your investigations.
Messages tab
On the Messages tab, you can see and reply to messages about the case from the Sophos MDR team.
- Messages that you send go into an MDR inbox. We'll respond to them later.
- Messages that you send or receive are copied to your authorized contacts' mailboxes, so you won't miss any messages.
- You can send and receive attachments as well as messages.
History tab
The History tab shows the history of all the activity on that case. For example, detections added, or changes in status, owner, and so on.
Troubleshoot cases
Cases are based on detections found in data that your devices upload to the Sophos Data Lake. These uploads are usually turned on by default. If you're not getting detections, check that they’re turned on.
To check that data’s uploaded from Sophos products, see Data Lake uploads. For data from third-party products, see About MDR and XDR integrations.