Detection rules
Detection rules let you specify how we handle threat detections.
You must be a Super Admin to use this feature.
Note
Currently, you can only use detection rules to suppress unwanted detections.
Suppressing detections
You might need to suppress detections that are false positives or recur too frequently. You can create rules to do this.
Rules can prevent detections that match a rule from doing the following:
- Showing in the list on the Detections page.
- Raising cases for further investigation.
Rules can suppress XDR cases that customers manage. They can't suppress MDR cases.
Create a detection rule
You can create a rule from an existing detection.
Note
You can create a maximum of 25 detection rules.
To create a rule, do as follows:
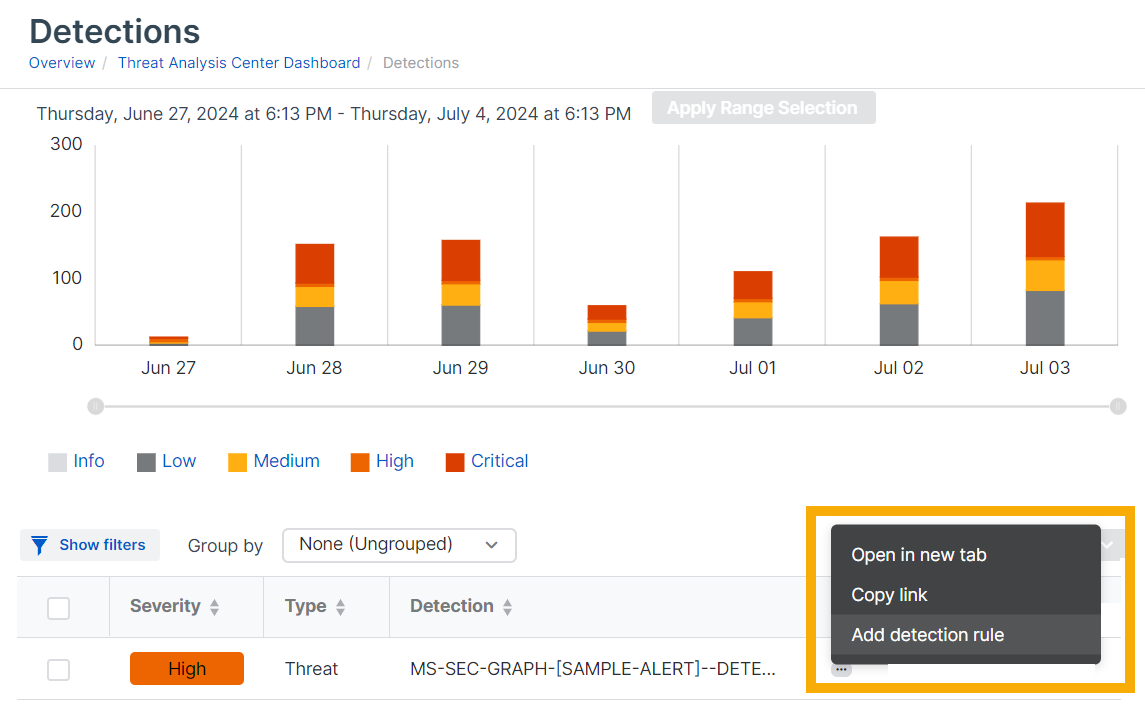
- Go to Threat Analysis Center > Detections.
-
Click the three dots
 next to a detection name in the list and select Add detection rule.
next to a detection name in the list and select Add detection rule. -
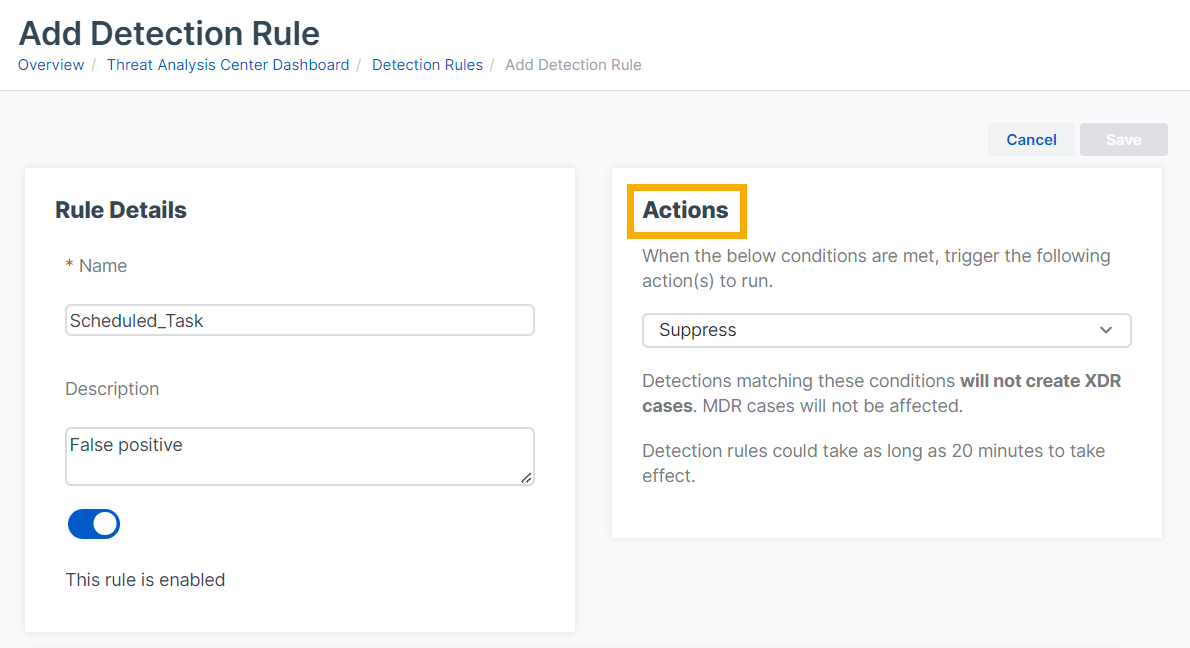
In the detection rule settings, do as follows:
- In Rule Details, enter a rule name and description. By default the rule is "enabled".
-
In Actions, select the action you want to take on detections.
Currently, you can only select Suppress. This prevents detections from being shown in the detection list and from generating cases.
-
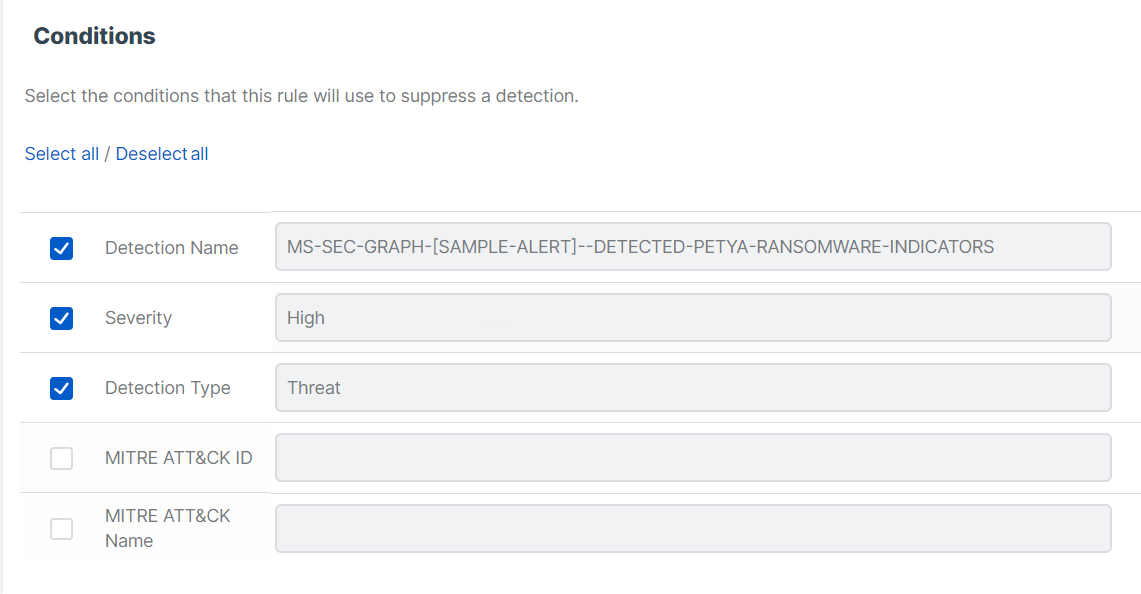
In Conditions, the characteristics of the threat that was detected, for example severity, are shown. Select characteristics that you want to use as conditions to trigger the rule.
-
Click Save.
A new detection rule can take 20 minutes to take effect.
A rule only applies to detections that occur after you've created the rule.
Note
The conditions that trigger a rule are case-sensitive. If a threat matches a condition, such as a command line, but uses different letter casing, for example "windows" instead of "Windows", the rule doesn't suppress the detection.
Turn detection rules on or off
To turn detection rules on or off, do as follows:
- Go to Threat Analysis Center > Detection rules.
- Click a detection rule's name to see its details.
-
In Rule details, click the toggle to turn the rule on or off.
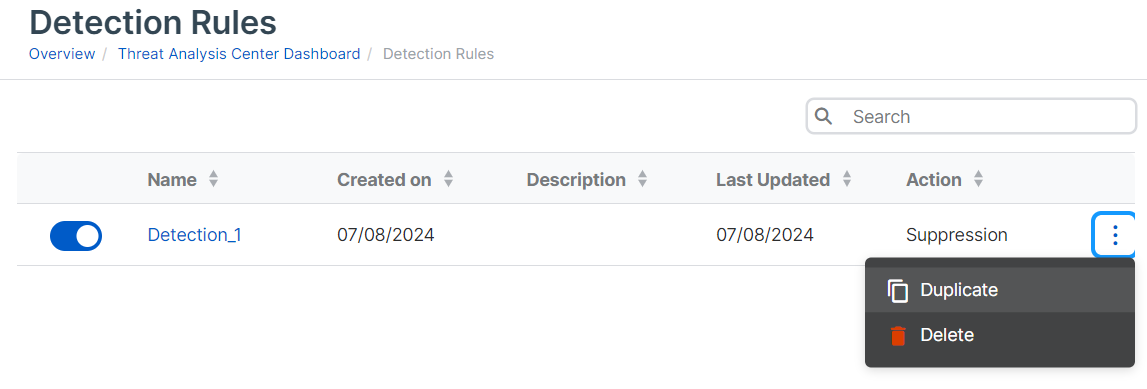
Duplicate and edit detection rules
You can't make changes to an existing rule.
You can duplicate a rule and make changes on the duplicate, as follows:
- Go to Threat Analysis Center > Detection rules.
- Find the rule and click the three dots
 in the rightmost column.
in the rightmost column. -
Select Duplicate.
You see a new rule with the same conditions and actions that you selected for the original rule.
-
Enter a name and description for the new rule.
- Select or clear checkboxes next to the conditions to edit the rule.
- Click Save.
Delete detection rules
To delete rules, do as follows:
- Go to Threat Analysis Center > Detection rules.
- Find the rule and click the three dots
 in the rightmost column.
in the rightmost column. - Select Delete.
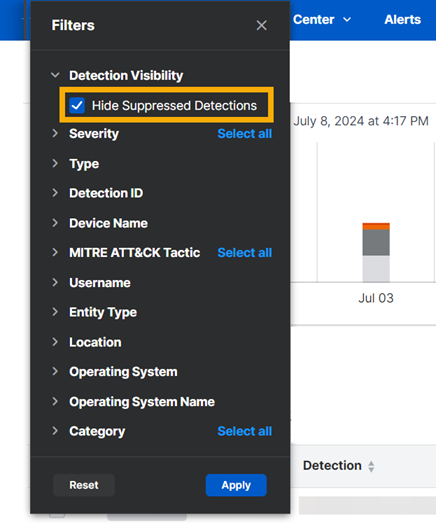
View suppressed detections
By default, detections that you've suppressed aren't shown in the Detections page.
If you want to see the suppressed detections, do as follows: