AWS CloudTrail
This AWS integration will be retired in the future. You can continue to use Sophos Cloud Optix to integrate AWS with Sophos Central while it remains supported. For more information, see Sophos Cloud Optix.
MSP Flex customers must have the Public Cloud integrations license pack to use this feature.
You can integrate AWS CloudTrail with Sophos Central so that it sends logs to Sophos for analysis.
Before you start
During the integration we give you commands to copy and run. You must run these commands in a local terminal with AWS CLI installed, or in AWS CloudShell. To find out how to set up AWS CLI, see Getting started with the AWS CLI.
You must run the commands as an IAM user with the "Administrator" role. If you don't have access to such an account, you can create a custom role with specific permissions. The permissions you need are in Custom role permissions.
Set up AWS CloudTrail integration
To integrate your AWS environment, do as follows:
- In Sophos Central, go to Threat Analysis Center and click Integrations.
-
Click AWS CloudTrail.
If you've already set up connections to AWS environments, you see them here.
-
Click Add. The Integration steps assistant takes you through the process of connecting to your AWS environment.
- In Step 1, choose whether you're using AWS Organisations or not.
- Choose to create new resources or use existing ones.
- Fill in the rest of the form with your AWS details.
- Click Save and continue.
- In Step 2, copy the
curlcommand. -
Go to a local terminal with AWS CLI installed, or to AWS CloudShell, and run the
curlcommand.This command downloads the integration script.
-
Go to Sophos Central.
- In Step 3, copy the integration command.
-
Go to a local terminal with AWS CLI installed, or to AWS CloudShell, and run the integration command.
The script integrates your AWS CloudTrail with Sophos Central.
-
Go to Sophos Central.
The AWS environment appears in the list.
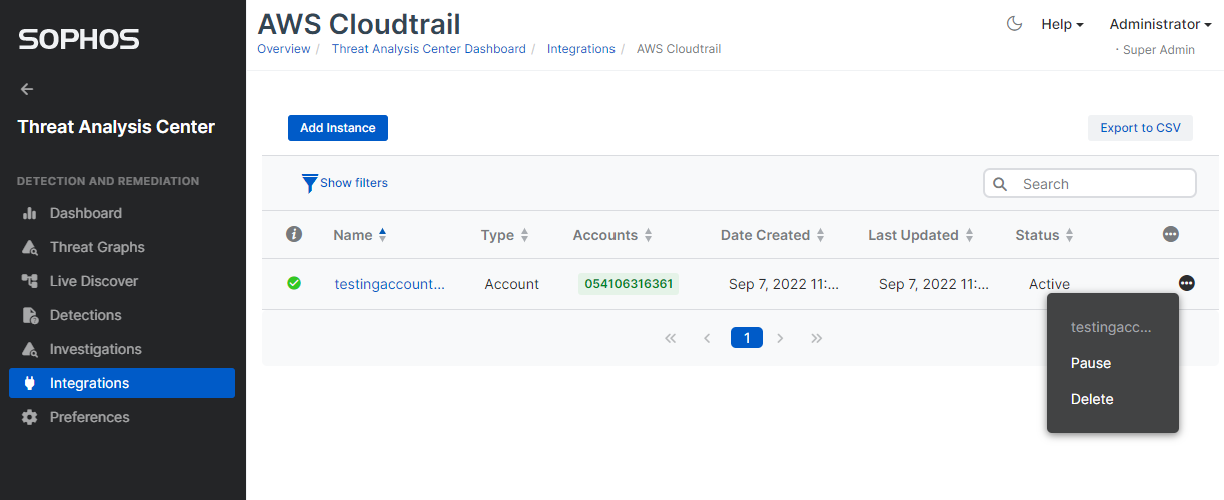
Manage AWS CloudTrail integrations
You can click the name of the AWS environment to edit settings.
Status shows the status of the integration with an AWS environment. This can be paused, active, disconnected, or deleted.
You can click the More icon and select actions, depending on the current status.
To delete a connection, click Delete. An assistant takes you through the process of deleting the connection, using AWS CLI commands.
When your Sophos license expires, your connections are paused. When you renew your license, the connections automatically become Active.
Include AWS Organizations accounts
If you're using AWS Organizations, you can choose which accounts to include in data collection.
- In Sophos Central, go to Threat Analysis Center > Integrations > Marketplace.
-
Click AWS CloudTrail.
A list of your integrations appears.
-
Click the name of the integration you want to change.
If you've many integrations, use the filter to list the integrations that use AWS Organizations.
-
In Edit Details > Accounts you can add a comma separated list of account IDs for which you want to collect data.
- Click Save.
We now only collect data from the AWS accounts in the list.
Custom role permissions
You can run the AWS commands we give you from an IAM user with the "Administrator" role.
If you want to set up a custom role instead, use the following permissions:
{
"Version": "2012-10-17",
"Statement": [
{
"Sid": "VisualEditor0",
"Effect": "Allow",
"Action": [
"iam:CreateRole",
"iam:AttachRolePolicy",
"iam:PutRolePolicy",
"iam:CreatePolicy",
"iam:PassRole",
"iam:DeleteRole",
"iam:DeleteRolePolicy",
"iam:GetPolicy",
"iam:GetPolicyVersion",
"iam:GetRole",
"iam:GetRolePolicy",
"iam:ListAttachedRolePolicies",
"iam:CreateServiceLinkedRole",
"iam:CreateInstanceProfile",
"iam:TagRole",
"tag:TagResources",
"ec2:DescribeRegions",
"s3:CreateBucket",
"s3:ListBucket",
"s3:PutBucketPolicy",
"s3:PutEncryptionConfiguration",
"s3:GetBucket*",
"s3:PutBucketTagging",
"s3:PutLifecycleConfiguration",
"s3:PutBucketNotification",
"s3:GetAccelerateConfiguration",
"sns:GetTopicAttributes",
"sns:CreateTopic",
"sns:DeleteTopic",
"sns:Subscribe",
"sns:AddPermission",
"sns:RemovePermission",
"sns:Unsubscribe",
"sns:TagResource",
"sns:SetTopicAttributes",
"sns:ListTagsForResource",
"sns:GetSubscriptionAttributes",
"sts:GetCallerIdentity",
"lambda:AddPermission",
"lambda:CreateFunction",
"lambda:GetFunction",
"lambda:GetPolicy",
"lambda:ListVersionsByFunction",
"lambda:TagResource",
"cloudtrail:CreateTrail",
"cloudtrail:DescribeTrails",
"cloudtrail:PutEventSelectors",
"cloudtrail:StartLogging",
"cloudtrail:UpdateTrail",
"cloudtrail:GetTrailStatus",
"cloudtrail:ListTags",
"cloudtrail:GetEventSelectors",
"cloudtrail:AddTags",
"cloudtrail:GetInsightSelectors",
"logs:CreateLogGroup",
"logs:PutLogEvents",
"logs:CreateLogStream",
"logs:CreateLogDelivery",
"logs:DeleteLogGroup",
"logs:DescribeLogGroups",
"logs:PutSubscriptionFilter",
"logs:PutRetentionPolicy",
"logs:ListTagsLogGroup"
],
"Resource": "*"
}
]
}