Cisco Meraki (Log collector)
You must have the Firewall integrations license pack to use this feature.
Note
An API-based integration of Cisco Meraki is also available. See Cisco Meraki (API).
You can integrate Cisco Meraki with Sophos Central so that it sends data to Sophos for analysis.
This integration uses a log collector hosted on a virtual machine (VM). Together they're called an appliance. The appliance receives third-party data and sends it to the Sophos Data Lake.
Note
You can add multiple Cisco Meraki firewalls to the same appliance.
To do this, set up your Cisco Meraki integration in Sophos Central, then configure one firewall to send logs to it. Then configure your other Cisco Meraki firewalls to send logs to the same Sophos appliance.
You don't have to repeat the Sophos Central part of the setup.
The key steps are as follows:
- Configure an integration for this product. This configures an image to use on a VM.
- Download and deploy the image on your VM. This becomes your appliance.
- Configure Meraki to send data to the appliance.
Requirements
Appliances have system and network access requirements. To check that you meet them, see Appliance requirements.
Configure an integration
To configure the integration, do as follows:
- In Sophos Central, go to Threat Analysis Center > Integrations > Marketplace.
-
Click Cisco Meraki.
The Cisco Meraki page opens. You can configure integrations here and see a list of any you've already configured.
-
In Data Ingest (Security Alerts), click Add Configuration.
Note
If this is the first integration you've added, we'll ask for details about your internal domains and IPs. See My domains and IPs.
Integration setup steps appears.
Configure the VM
In Integration setup steps you configure your VM as an appliance to receive data from Meraki. You can use an existing VM, or create a new one.
To configure the VM, do as follows:
- Enter an integration name and description.
-
Enter a name and description for the appliance.
If you've already set up a Sophos appliance, you can choose it from a list.
-
Select the virtual platform. Currently we support VMware ESXi 6.7 Update 3 or later and Microsoft Hyper-V 6.0.6001.18016 (Windows Server 2016) or later.
-
Specify the IP settings for the Internet-facing network ports. This sets up the management interface for the VM.
-
Select DHCP to assign the IP address automatically.
Note
If you select DHCP, you must reserve the IP address.
-
Select Manual to specify network settings.
-
-
Select the Syslog IP version and enter the Syslog IP address.
You'll need this syslog IP address later, when you configure Meraki to send data to your appliance.
-
Select a Protocol.
You must use the same protocol when you configure Meraki to send data to your appliance.
-
Click Save.
We create the integration and it appears in your list.
In the integration details, you can see the port number for the appliance. You'll need this later when you configure Meraki to send data to it.
It might take a few minutes for the VM image to be ready.
Deploy the VM
Restriction
If you're using ESXi, the OVA file is verified with Sophos Central, so it can only be used once. If you have to deploy another VM, you must create an OVA file again in Sophos Central.
Use the VM image to deploy the VM. To do this, do as follows:
- In the list of integrations, in Actions, click the download action for your platform, for example Download OVA for ESXi.
- When the image download finishes, deploy it on your VM. See Deploy a VM for integrations.
Configure Cisco Meraki
To configure Meraki to send data to your appliance, do as follows.
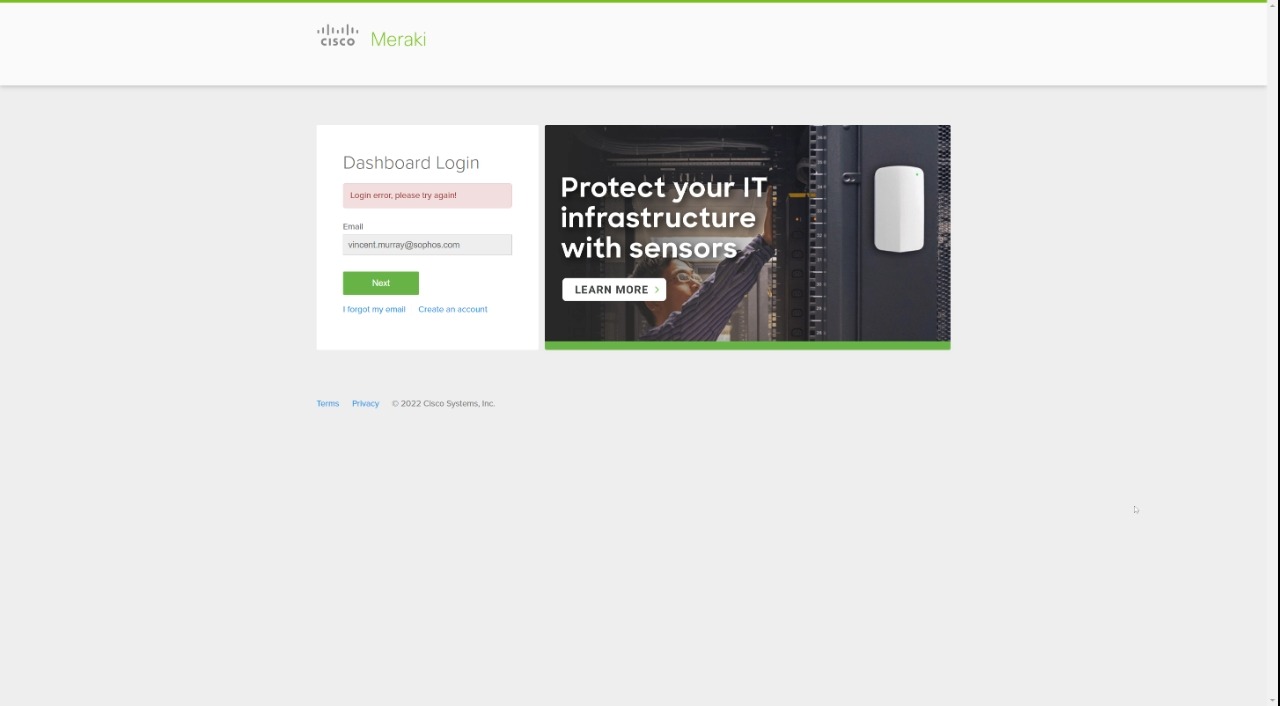
- Sign in to the Meraki Dashboard.
- Click Network-wide > Configure > General.
- Scroll down to Reporting and click Add a syslog server.
-
Enter the following connection details for your appliance:
- IP address. This is the syslog IP address you set in Sophos Central.
-
Port number.
You must enter the same settings you entered in Sophos Central when you added the integration.
-
Add the following roles to configure the data sent to your appliance:
- Event logs for the services running on your devices. For example
Security events,Appliance event log. Flows. These are traffic flow messages that include source and destination information, and port numbers.IDS Alerts. These are alerts from the intrusion detection system.
- Event logs for the services running on your devices. For example
-
In You have unsaved changes, click Save.
If the Flows role is enabled on an MX security appliance, logging for individual firewall rules can be turned on or off on the Security appliance > Configure > Firewall page, in the Logging column.
More resources
This video takes you through setting up the integration.
For more information on configuring syslog servers on Meraki devices, refer to the Cisco documentation. See Syslog Server Overview and Configuration.