Remote access IPsec group authentication
The Sophos Connect client supports local and Active Directory (AD) users and groups.
If you haven't configured remote access IPsec VPN, it's turned off by default for all groups.
If you've configured remote access IPsec, it's turned off by default for AD groups that you import to Sophos Firewall. It's also turned off for groups that you migrate, for example, from an earlier version of Sophos Firewall. However, when you create a new local group on Sophos Firewall, IPsec remote access is turned on by default.
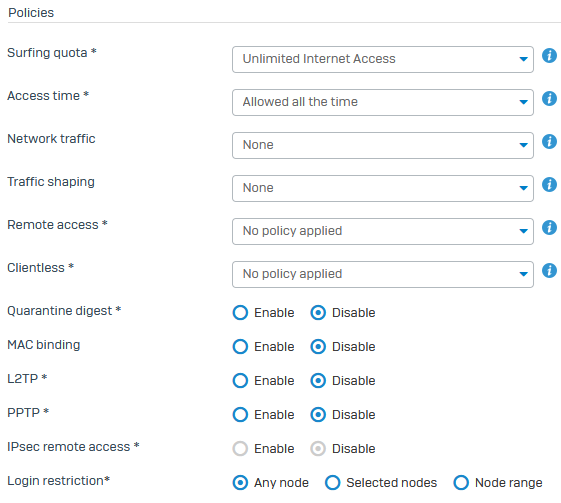
You can check this setting under Authentication > Groups.
The following image shows a group with remote access IPsec turned off.
Remote access IPsec VPN uses the Sophos Connect client. If a remote user, for example, an AD user, wants to sign in to the Sophos Connect client for the first time, they must first sign in to another authentication client, such as the user portal.
If a user is a member of multiple groups, the policy from the group at the top of the list is applied.
If you change the settings for a group, they override the remote access IPsec settings.
If you turn off remote access IPsec for a group, all the users are disconnected. They won't be able to reconnect, and they'll see an authentication error.
User policies always take priority over group policies. For example, if you turn off the remote access IPsec for an AD group, then turn it on for a user in that group, the user can sign in.
Note
If you turn on remote access IPsec for a group, you can't turn it off for a user in that group.