Firewall rules
With firewall rules, you can allow or disallow traffic flow between zones and networks. You can implement policies and actions to enforce security controls and traffic prioritization.
You can create firewall rules for IPv4 and IPv6 networks. You can implement the following actions through firewall rules:
Access and logging
- Allow, drop, or reject traffic based on the matching criteria, which include source, destination, services, and users during the specified time period.
- Create linked (source) NAT rules for address translation.
- Log traffic that matches the rule criteria.
Policies and scanning
- Apply policies for web traffic, application control, and IPS.
- Implement web proxy filtering with decryption and scanning.
- Send content for Zero-day protection analysis.
- Enforce malware scanning for web, email, and FTP traffic.
- Enforce action on endpoint devices and servers with a Synchronized Security heartbeat, which sends information about their health status to Sophos Firewall.
Traffic prioritization
- Apply bandwidth controls.
- Prioritize traffic with DSCP marking.
You don’t require a firewall rule for system-generated traffic or to allow access to system services. To specify access to system services from certain zones, go to Administration > Device access.
- To add a firewall rule manually, select Add firewall rule and then select New firewall rule.
- To create destination NAT rules along with firewall rules automatically, select Add firewall rule and then select Server access assistant (DNAT).
Server access assistant (DNAT)
Create DNAT rules to translate incoming traffic to servers, such as web, mail, SSH, or other servers, and access remote desktops. The assistant also creates a reflexive SNAT rule (for outbound traffic from the servers), a loopback rule (for internal users accessing the servers), and a firewall rule (to allow inbound traffic to the servers) automatically.
Rules and rule groups
You can create firewall rules and add them to rule groups.
Sophos Firewall evaluates firewall rules, not rule groups, to match criteria with traffic. It uses the matching criteria of rule groups only to group firewall rules.
Default rules
Sophos Firewall creates default rule groups containing a firewall rule to drop traffic going to WAN, DMZ, and internal zones (LAN, Wi-Fi, VPN, and DMZ). These rules are turned off by default.
A firewall rule for email MTA is automatically created along with a linked NAT rule when you turn on MTA mode. MTA mode is turned on by default.
Note
Review rule positions after a firewall rule is created automatically or manually to make sure the intended rule matches traffic criteria.
Automatically created firewall rules, such as those for email MTA, IPsec connections, and hotspots, are placed at the top of the firewall rule list and are evaluated first. Later, if you manually create a firewall rule with Rule position set to Top or another automatically created rule, these are placed at the top of the rule table, changing rule positions. The policies and actions of the rule at the top will apply, which may lead to unplanned outcomes, such as failure in mail delivery or tunnels not being established, when matching criteria for the new and existing rules overlap.
The default Drop all rule is assigned ID 0. The rule drops traffic that doesn’t match the criteria of any firewall rule. It's positioned at the bottom of the rule table. You can’t edit, delete, or move this rule. It doesn’t show the usage count. Filters don't apply to it.
Rule groups
You can’t create rule groups without a firewall rule. So, create a rule group when you create a rule from the rule template or with an existing rule from the rule table.
You can add a firewall rule to a rule group or detach it from the group. Empty rule groups can't exist. When you delete the last rule from a rule group, the rule group is deleted.
Rule table actions
- To see IPv4 or IPv6 rules in the rule table, select IPv4 or IPv6.
- To hide or show the rule filter, select Disable filter and Enable filter, respectively.
-
To turn on or turn off rules or rule groups, select them and click Enable or Disable.
If you select a combination of turned on and turned off rules, you can't perform these actions.
-
To delete rules or rule groups, select them and click Delete.
-
To filter the rules by any rule parameter, click Add filter and then select a field name and its option.
When you apply the filter, you can't select a rule group because groups may contain a combination of turned on and turned off rules. However, you can select individual rules.
-
To reset the rule filter, click Reset filter.
- To view the rule details in the rule table, pause over the icons under Feature and service.
- To edit a rule group, click Edit
 .
. -
Hash (#) indicates the rule position. To change the position of a rule or rule group, click and drag the Rule handle (
 ). Sophos Firewall evaluates rules from the top down until it finds a match. Once it finds a match for the packet, it doesn’t evaluate subsequent rules. So, position the specific rules above the less specific rules.
). Sophos Firewall evaluates rules from the top down until it finds a match. Once it finds a match for the packet, it doesn’t evaluate subsequent rules. So, position the specific rules above the less specific rules.You can change the position of a rule within the rule group. To change its position beyond the group, detach the rule from the group or change the position of the group.
Click More options  to specify the following rule actions:
to specify the following rule actions:
- To turn on or turn off a rule, select the switch.
-
To reset the count for the data transferred, select Reset data transfer count. This is useful when troubleshooting.
To see the data transferred using a rule, go to Reports > Dashboards. Select Traffic dashboard and scroll down to Allowed policies.
-
To move a rule to a different position in the table, enter the position number next to Move To and press
Enter.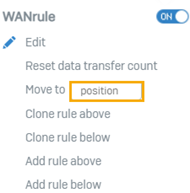
-
To edit or delete a rule, select the action.
- To clone or add a rule next to an existing rule, select the action.
-
To detach a firewall rule from a group, select Detach.
Rule group actions: Click More options
 next to a rule to specify rule group actions.
next to a rule to specify rule group actions. -
You can create a rule group for rules that aren’t attached to a rule group. Select New group under Add to group next to the rule. Enter a group name and specify the rule type and the source and destination zones.
- To add a rule to a rule group, select a group or add a new group.
- To delete a rule group, click Delete
 .
.
Linked NAT rules
These are source NAT rules and are listed in the NAT rule table. You can identify them by the firewall rule ID and name.
Sophos Firewall applies firewall rules before it applies source NAT rules. If a NAT rule above the linked rule meets the matching criteria, Sophos Firewall applies that rule and doesn’t look further for the linked rule. However, linked NAT rules apply only to traffic that matches the firewall rule they are linked to.
You can unlink a linked NAT rule from the NAT rule table. Once you unlink the rule from the original firewall rule, you can edit the NAT rule. It will now be evaluated independent of the original firewall rule based on its criteria and not the original firewall rule criteria.
Rule status
| Status | Description |
|---|---|
| Unused | Didn’t find matching traffic during the past 24 hours. |
| Disabled | Turned off manually. |
| Changed | Updated during the past 24 hours. |
| New | Created during the past 24 hours. |
Rule table icons
| Icons | Description |
|---|---|
 | User rule |
 | Match known users not selected. |
 | Rule turned off. |
 | Action set to Accept. |
 | Rule turned off. |
 | Action set to Drop or Reject. |
 | Rule turned on. |
 | Action set to Accept. |
 | Rule turned on. |
 | Action set to Drop or Reject. |
   | Turned off: Scanning for web, FTP, or email traffic. Web proxy (DPI is turned on). Traffic logging. |
    | Policy set to None: Web policy, application control, intrusion prevention, traffic shaping. |
 | Turned off or has no restriction: Security Heartbeat. |
    | Turned on: Scanning for web, FTP, or email traffic. Web proxy. Exclusions to firewall rule. Traffic logging. |
  | Policy specified: IPS, traffic shaping |
  | Policy set to Accept: Web policy, application control |
 | Policy set to malware and PUA detection: Security Heartbeat |
 | No restriction and set to malware and PUA detection: Security Heartbeat |
  | Policy set to Drop: Web policy, application control |
 | Policy set to PUA detection: Security Heartbeat |
 | No restriction and set to PUA detection: Security Heartbeat |
  | Policy set to Deny: Web policy, application control policy |
 | No restriction and no heartbeat: Security Heartbeat |
NAT and routing migration
NAT configuration
When you migrate from an earlier version to SFOS 18.0 and later, Sophos Firewall migrates the NAT settings of firewall rules as NAT rules and lists them in the NAT rule table. It no longer offers gateway-based NAT configuration.
Sophos Firewall uses the firewall rule ID to match traffic with migrated NAT rules. For details of NAT migration from versions earlier than SFOS 18.0, go to NAT rules.
Routing configuration
In SFOS 18.0 and later versions, you need to specify routing policies in SD-WAN policy routing. Firewall rules no longer include routing settings. When you migrate from an earlier version, Sophos Firewall migrates the routing settings in firewall rules as Migrated SD-WAN policy routes. You can see them in the SD-WAN policy routing table. You can identify these migrated policy routes by the firewall rule ID and name.
Sophos Firewall uses the firewall rule ID to match traffic with migrated routes. For details of policy route migration from versions earlier than SFOS 18.0, go to Migrated SD-WAN policy routes.
Migrated firewall rules: Rule behavior
In SFOS 17.5 and earlier, although business application rules and user-network rules were listed in a single rule table, Sophos Firewall evaluated these rule types independently to find matching criteria.
For system-destined traffic (example: accessing Sophos Firewall services) and incoming traffic (example: traffic to internal servers) that matched a destination NAT rule, it ignored user-network rules and matched the traffic with business application rules.
From SFOS 18.0, Sophos Firewall has removed the distinction between business application and user-network rules. It now offers both as firewall rules. To ensure that the consolidation does not affect the rule-matching behavior of earlier versions, it will continue to ignore migrated user-network rules positioned above migrated business application rules for system-destined and incoming traffic.
Web server rules and protection policies: Sophos Firewall has merged some protection categories into a single category, mapped filter rules to new rule IDs, and introduced filtering strength levels. For details, go to protection policies for web servers.
More resources