Create a policy-based IPsec VPN connection using preshared key
You can create and set up an IPsec VPN between the head office and a branch office.
Introduction
You must configure the following on the head office and the branch office firewalls.
- Prerequisite: Configure IP hosts for the local and remote subnets.
- Configure the IPsec VPN connection.
- Optional: Edit the automatically created firewall rule to create an independent rule for outbound traffic.
- Optional: Create a firewall rule for inbound traffic if you want independent firewall rules.
- Allow access to services.
- Check connectivity.
In this example, we've used a preshared key for authentication.
Define LANs at the head office
Create hosts for the head office and branch office networks at the head office.
- Go to Hosts and services > IP host and click Add.
-
Create a host for the head office LAN.
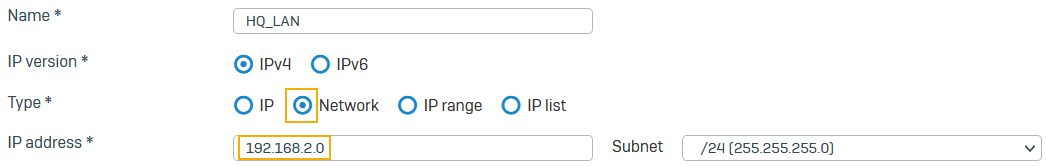
-
Click Save.
- Click Add.
-
Create a host for the branch LAN.
-
Click Save.
Add an IPsec connection at the head office
Create and activate an IPsec connection at the head office. The connection specifies endpoint details, network details, and a preshared key.
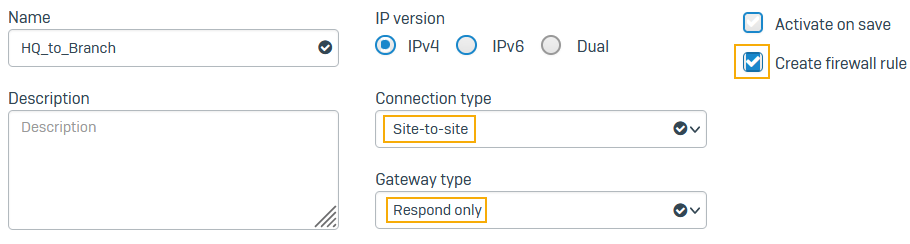
- Go to Site-to-site VPN > IPsec and click Add.
-
Specify the general settings. To create a firewall rule for the connection, select Create firewall rule.
-
Specify the encryption settings.
Note
Make a note of the preshared key. You'll need it later when you're configuring the branch office connection.

-
Specify the local gateway settings.
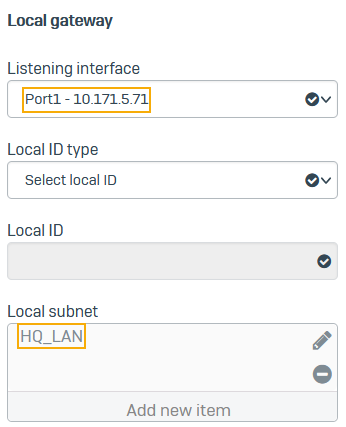
-
Specify the remote gateway settings. To establish the connection with any of the remote gateway's interfaces, specify a wildcard (
*). You must use the same preshared key for all IPsec connections that use a wildcard remote gateway address on the firewall.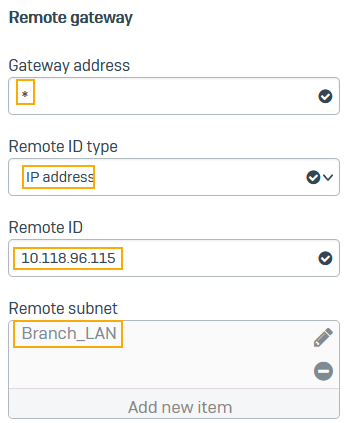
-
Click Save.
The connection appears on the list of IPsec connections.
-
Click the status button
 to activate the connection.
to activate the connection.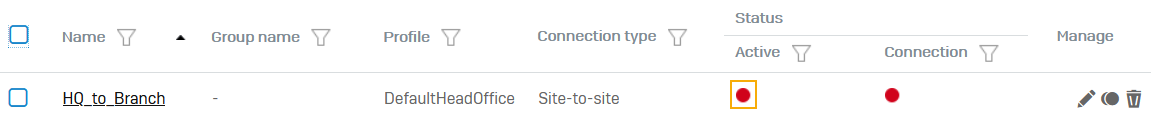
Edit the firewall rule
Edit the firewall rule created when you created the IPsec connection if you want to configure a rule for outbound VPN traffic.
-
Go to Rules and policies > Firewall rules and click the
IPsec HQ to Branchrule.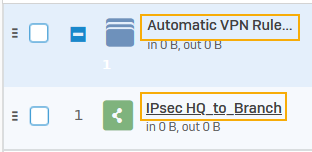
-
Change the name of the rule to outbound VPN traffic if you want.
-
Specify the settings.
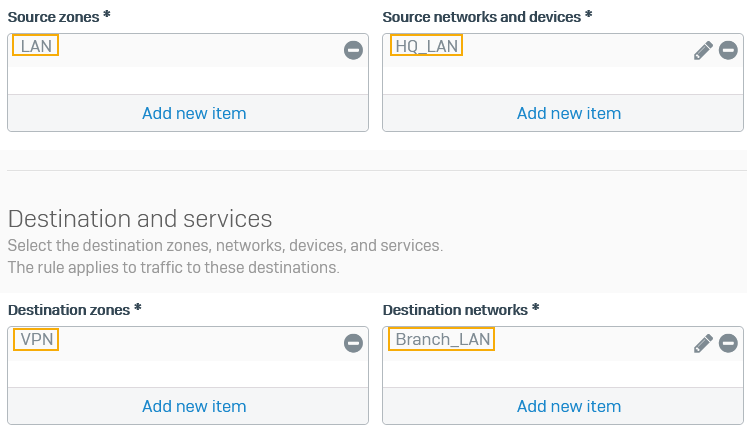
-
Click Save.
Add a firewall rule
Create a rule for inbound VPN traffic.
- Go to Rules and policies > Firewall rules, select protocol IPv4 or IPv6, and click Add firewall rule. Select New firewall rule.
-
Specify the settings.
Setting Value Rule name Inbound VPN trafficSource zones VPN Source networks and devices Branch_LANDestination zones LAN Destination networks HQ_LAN -
Click Save.
Allow access to services on the head office firewall
- Go to Administration > Device access.
- Under Ping/Ping6, select VPN. Users can ping the firewall's IP address through VPN to check connectivity.
- Click Apply.
Define LANs at the branch office
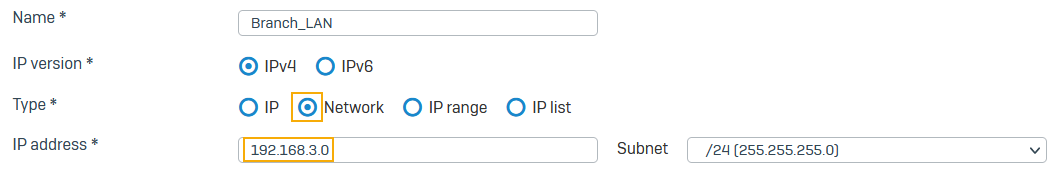
Create the hosts for the branch office and head office networks at the branch office.
- Go to Hosts and services > IP host and click Add.
-
Specify the local LAN settings.
Setting Value Name Branch_LANType Network IP address 192.168.3.0 -
Specify the remote LAN settings.
Setting Value Name HQ_LANType Network IP address 192.168.2.0
Add an IPsec connection at the branch office
You create and activate an IPsec connection at the branch office.
- Go to Site-to-site VPN > IPsec and click Add.
-
Specify the general settings:
Setting Value Name Branch_to_HQConnection type Site-to-Site Gateway type Initiate Create firewall rule Enabled -
Specify the encryption settings.
Setting Value Profile Branch office (IKEv2)Authentication type Preshared key -
Type and confirm the preshared key.
Note
Make sure to use the same preshared key as in the head office.
-
Specify the local gateway settings.
Setting Value Listening interface Port1 – 10.118.96.115Local subnet Branch_LAN -
Specify the remote gateway settings.
Setting Value Gateway address 10.171.5.71Remote ID IP address – 10.171.5.71Remote subnet HQ_LAN -
Click Save. The connection appears in the list of IPsec connections.
- Click Status
 to activate the connection.
to activate the connection.
Edit the firewall rule
Edit the firewall rule created when you created the IPsec connection if you want to configure a rule for outbound VPN traffic.
- Go to Rules and policies > Firewall rules and click the
IPsec Branch to HQrule. -
Specify the settings.
Setting Value Rule name Outbound VPN trafficSource zones LAN Source networks and devices Branch_LANDestination zones VPN Destination networks HQ_LAN -
Click Save.
Add a firewall rule
Create a rule for inbound VPN traffic.
- Go to Rules and policies > Firewall rules, select protocol IPv4 or IPv6, and click Add firewall rule. Select New firewall rule.
-
Specify the settings.
Setting Value Rule name Inbound VPN traffic Source zones VPN Source networks and devices HQ_LANDestination zones LAN Destination networks Branch_LAN -
Click Save.
Allow access to services
- Go to Administration > Device access.
- Under Ping/Ping6, select VPN.
Users can ping the firewall's IP address through VPN to check connectivity.
- Click Apply.
Check connectivity
You check the connectivity from the head office to the branch office and vice versa.
- From the head office, check that you can ping the branch office. For example, on Windows, start a command prompt and type the following command:
ping 192.168.3.0 - From the branch office, check that you can ping the head office. For example, on Windows, start a command prompt and type the following command:
ping 192.168.2.0 - From the head office, click Firewall and view the traffic.
- From the branch office, click Firewall and view the traffic.
Head office and branch office configurations
In a head and branch office configuration, the branch office firewall usually acts as the tunnel initiator and the head office firewall as a responder due to the following reasons:
- When the branch office firewall is configured with a dynamic IP address, the head office device can't start the connection.
- As there can be many branch offices, we recommend that each branch office retry the connection instead of the head office retrying all connections to branch offices.
More resources