Security management and best practices
Sophos Firewall makes it easy to configure and manage everything needed for modern protection and from a single screen.
You can easily view and set security and control policies for the DPI engine AV scanning, sandboxing and threat intelligence file analysis, IPS, traffic shaping, web and application control, and Security Heartbeat all in one place. You can do all this on a rule-by-rule, user-by-user, or group-by-group basis.
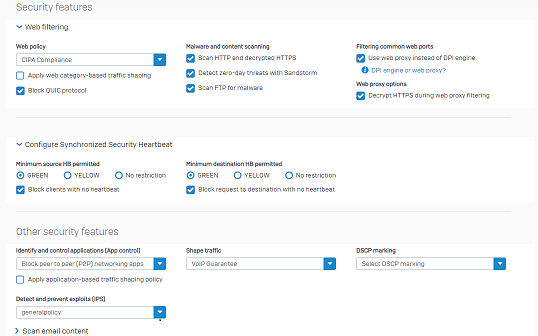
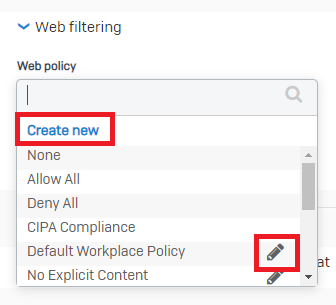
Web protection and control are the main features of any firewall. We've implemented a top-down inheritance policy model, which makes building sophisticated policies easy and intuitive.
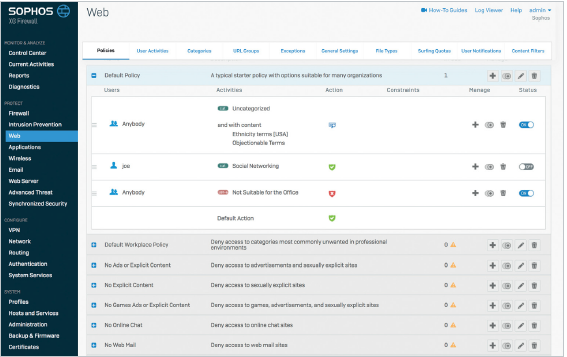
We include pre-defined policy templates for common deployments. You can then customize these if you need to. You can create new policies and edit existing ones directly from the firewall rule.
You can configure firewall rules in many ways, depending on your network configuration. However, we recommend you follow best practices when configuring Sophos Firewall to protect your network.
Segregate your networks and apply IPS policies
Separate your networks so any internet-facing services, such as web servers or remote access servers, are on a network segment and zone other than your main LAN network. Place internet-facing services such as these in a DMZ zone and configure firewall rules to block connections from the DMZ to the LAN.
You can also segment other LAN zones as required by using smaller subnets, assigning these to separate LAN zones, and configuring firewall rules to manage traffic between these networks.
In the following example, the network isn't segmented, allowing the infection to spread easily between endpoints.
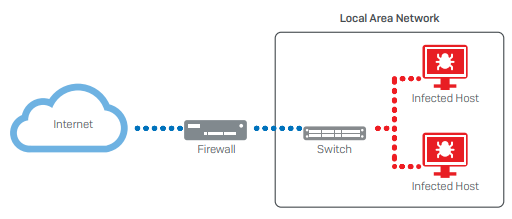
Sophos Firewall prevents infection in one area from spreading to other areas by separating the network into segments, such as the DMZ and LAN networks.
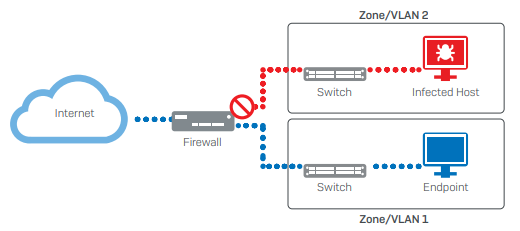
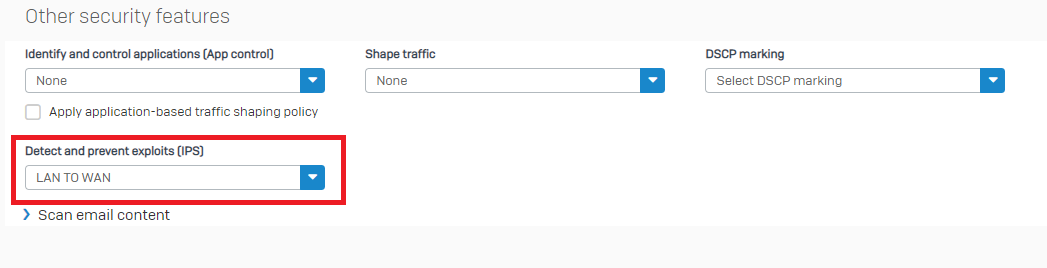
Doing this and applying an IPS policy to rules that govern traffic between these networks reduces the risk of malware or hackers being able to move laterally through your networks if they do manage to perform a successful initial attack. It also provides more time for the threat to be detected and mitigated.
Lock down remote access
Where possible, only allow access to internal resources over a VPN connection and don't use port forwarding. If you must use port forwarding, make sure you apply an IPS policy to the rule-handling traffic.
Configure SSL/TLS inspection rules
Configure an SSL/TLS inspection rule to scan most network traffic, with exceptions configured only for services to which SSL scanning will cause problems.
For further details about SSL/TLS inspection rules and how to configure them, see SSL/TLS inspection rules.
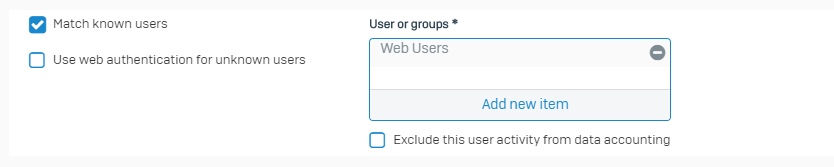
Only allow authenticated users to connect to the internet from your LAN
When configuring firewall rules to handle user traffic, make sure that you select Match known users. This ensures that only authenticated users can access external resources from within your LAN network.
Only use NAT for those services that are explicitly needed
Network Address Translation (NAT) allows you to pass traffic easily between different networks. However, only configure NAT rules for services that require it and not for ANY service. Doing this cuts down the surface area malware or hackers can target if one part of your network is breached.
For further information about NAT rules and how to configure them, see NAT rules.
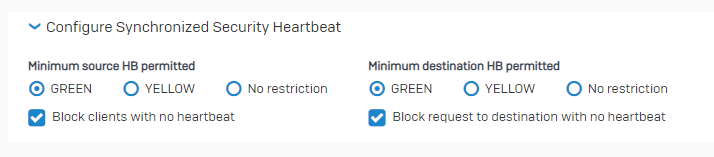
Isolate the infected system automatically
Use Security Heartbeat to monitor systems and automatically isolate those that show signs of infection or compromise. Security Heartbeat stops the compromised systems from connecting to others on your network and clean systems from connecting to those that may have been compromised.