Log settings
Sophos Firewall provides event logs for traffic, system, and network protection functions. You can use logs to analyze network activity and identify security issues.
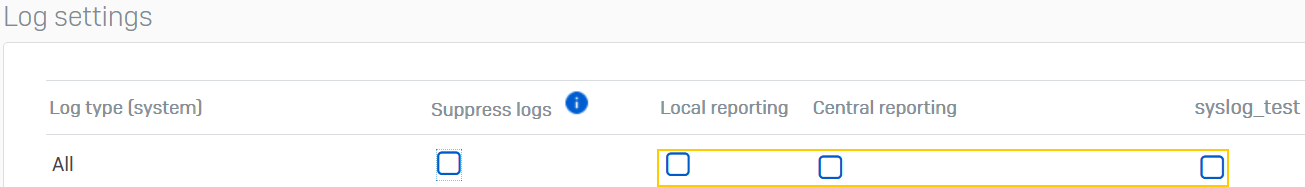
To see or change log settings, go to System services > Log settings.
Event logs
You can select the log types to store the logs locally and see them in the Log viewer or send them to Sophos Central or external syslog servers.
You can select logs to store or send by module or feature, or you can select all logs.
-
To save the logs for traffic matching the following rules, do as follows:
- Firewall rules: Select Log firewall traffic in each rule.
- SSL/TLS inspection rules: Select Log connections in each rule.
-
To make sure the saved logs are shown locally or sent externally, go to System services > Log settings and select the log types under Log settings as follows:
- Log viewer: Under Local reporting
- Sophos Central: Under Central reporting
- Syslog servers: Under the syslog servers you configure
Locally
To store event logs locally and show them in the Log viewer, select the log types under Local reporting.
Note
These logs are shown in the log viewer. They aren't on-box reports. To turn reporting on or off, see Continuous generation of application reports.
Central reporting
To send logs to Sophos Central, you must go to the Sophos Central page and turn on Sophos Central services. See Sophos Central services overview.
On the Log settings page, you can change the log types to send to Sophos Central under Central reporting.
The selection only applies to logs. It doesn't apply to reports.
Syslog servers
You can configure up to five syslog servers to send the event logs to. The firewall sends these logs to the servers. The syslog protocol normally uses UDP port 514 for communication.
Syslog servers provide a central logging facility and long-term protected storage for event logs.
To send logs to a syslog server, click Add and specify the syslog server details. The syslog server appears on the log settings page.
Note
Establishing a TLS connection with the syslog server in LINCE mode requires the certificate's Common Name (CNAME) or Subject Alternative Name (SAN) to match the syslog server's domain. If LINCE is turned off, the firewall only verifies the CNAME.
Log suppression
You can suppress logs, eliminating multiple consecutive log entries for an event. Log suppression saves logging space and processing cycles.
The feature applies to logs sent to the log viewer, Sophos Central, and third-party syslog servers.
- Under Suppress logs, select All to suppress all logs. Currently, you can only suppress the logs under Firewall.
- You can see the number of log entries for an event under Log occurrence in the log viewer.
Log type
Firewall: Information about traffic associated with the firewall configuration, such as firewall rules, MAC filtering, and DoS attacks.
IPS: Logs of detected and dropped attacks based on unknown or suspicious patterns (anomalies) and signatures.
Antivirus: Details of viruses detected in HTTP, SMTP, FTP, POP3, IMAP4, HTTPS, SMTPS, IMAPS, and POPS traffic.
Anti-spam: Details of SMTP, POP3, IMAP4, SMTPS, POPS, IMAPS spam, and probable spam emails.
Content filtering: Details of web and application filtering events, such as those associated with web policies.
Note
To view events associated with a web policy, you must select Log firewall traffic in the associated firewall rule.
Events: Information about configuration, authentication, and system activities.
Web server protection: Details of web server protection activities, such as protection policies.
Active threat response: Information about logged and blocked traffic based on MDR threat feeds and Sophos X-Ops threat feeds.
Wireless: Details of access point activity and SSIDs.
Note
Under Local reporting, Access points & SSID selection is turned off by default because wireless logs aren't available in the Log viewer. You can see wireless logs if you send them to Sophos Central or syslog servers.
Heartbeat: Information about the health status of the endpoints.
System health: Details of CPU usage, memory usage, number of live users, interfaces, and disk partitions.
Zero-day protection: Logs of all Zero-day protection events.
SD-WAN: Logs of SD-WAN profile, SLA, and route usage.