Authentication
You can set up authentication using an internal user database or third-party authentication service. To authenticate themselves, users must have access to an authentication client. However, they can bypass the client if you add them as clientless users. The firewall also supports two-factor authentication, transparent authentication, and guest user access through a captive portal.
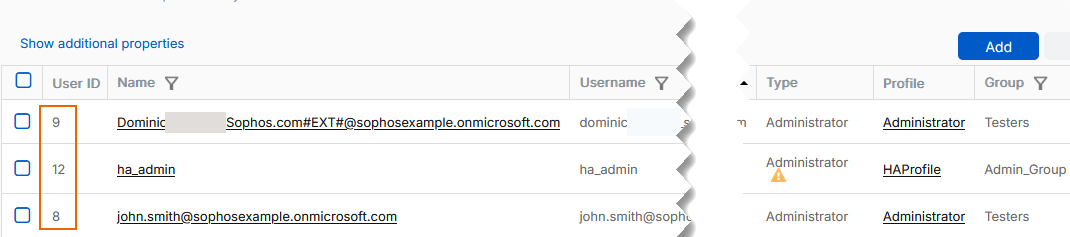
User IDs
The firewall supports a maximum of 65,535 user IDs shared across users and groups.
You can create users beyond this limit, but users with assigned IDs higher than 65,535 may experience functional issues, such as being unable to download the .ovpn configuration files from the VPN portal.
To prevent such issues, we recommend regularly deleting unused or inactive users and groups so their IDs can be reused.
More resources