Manually configure OTP tokens
You can manually configure the secret for hardware and software tokens and assign it to users.
The firewall supports SHA1, SHA256, and SHA512 hash algorithms.
Configure MFA settings
If you haven't already configured MFA settings, do as follows:
- Go to Authentication > Multi-factor authentication.
- For One-time password, select Specific users and groups.
-
Click Add new users and groups, select the users and groups, and click Apply selected items.
-
Don't turn on Generate OTP token with next sign-in.
The firewall won't generate QR codes. Users can use the hardware token or the one-time passcode you share with them.
They can also manually enter the secret in their authenticator apps. Users who've already scanned the QR code can continue to use the passcode the app generates.
Note
You must use a hash algorithm that your authenticator app supports. If you use an authenticator app that doesn't support SHA256 or SHA512, such as Microsoft Authenticator, you can still scan the QR code, but the sign-in fails.
We recommend you use an authenticator app that supports SHA256 and SHA512, such as Sophos Intercept X or Google Authenticator.
-
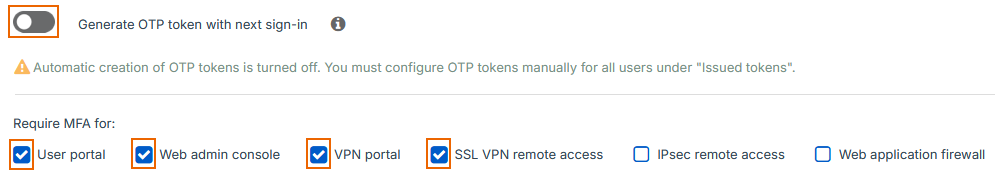
Select the services that require MFA.
We select User portal, Web admin console, VPN portal, and SSL VPN remote access in this example.
-
For OTP hash algorithm, select a hash algorithm.
- For OTP timestep settings, enter the timestep (time period) value your hardware token or authenticator app requires.
- Click Apply.
Add a token
To manually create a token, do as follows:
- Go to Authentication > Multi-factor Authentication.
- Under Issued tokens, click Add token (for hardware tokens).
- For OTP hash algorithm, select a hash algorithm.
-
For Secret, enter as follows:
- For hardware tokens, enter the key the device manufacturer provides.
-
For software tokens, enter a unique hexadecimal value. The authenticator app will use the secret to generate passcodes.
Go to a third-party website and convert the hexadecimal secret to Base32. For example, go to Cryptii. Share the Base32 secret with the user.
Users can manually enter the secret in their authenticator app to generate the OTP. See See Generate OTPs and sign in.
-
Select the user.
- This example configuration uses the Default token timestep value under MFA settings rather than a custom timestep.
- Click Save.