Firewall health check
The firewall implements network security policies based on recommended configurations, best practices, and regulatory standards, including those outlined by the Center for Internet Security (CIS). The firewall continuously checks configurations, such as firewall rules, password complexity, multi-factor authentication (MFA), and other settings, to ensure they comply with these policies.
The data is updated when any monitored configuration changes.
We recommend ensuring that all configurations are compliant for enhanced network security.
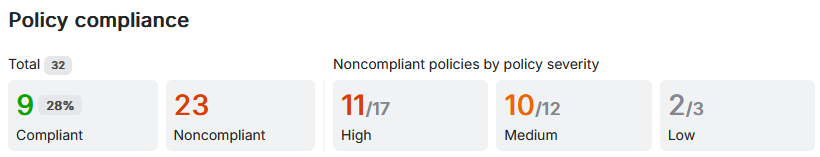
Policy compliance
You can monitor the total number of checked configurations and the number of compliant and noncompliant configurations.
The noncompliant configurations are shown by severity, depending on the network security risk they pose. You can fix them or manually set their status to compliant without fixing them. To fix the noncompliant configurations, you must meet the policy's requirements.
- Compliant: The number of configurations that comply with the firewall's network security policies. This is also shown as a percentage of the total number of checked configurations.
- Noncompliant: The number of configurations that don't comply with the firewall's network security policies. They're categorized based on severity.
You can search for a specific policy, module, standard, or severity using the search field.
You can sort the policy compliance details by clicking the specific column.
The firewall shows the policy compliance details as follows:
| Name | Description |
|---|---|
| Policies | The firewall's network security policies. Your firewall configurations are checked against these policies for compliance. Based on your configuration, the policy status is shown as follows:
|
| Module | The firewall module that the policy relates to. |
| Standard | The industry standard or best practice configuration that the policy is based on:
|
| Severity | The policy compliance category, depending on the network security risk policies pose. The severity categories are as follows:
|
| Status | Shows whether your firewall configuration complies with the policy or not. The statuses are as follows:
|
| Action | Actions that you can take for policies that your firewall configurations don't comply with. The options are as follows:
|