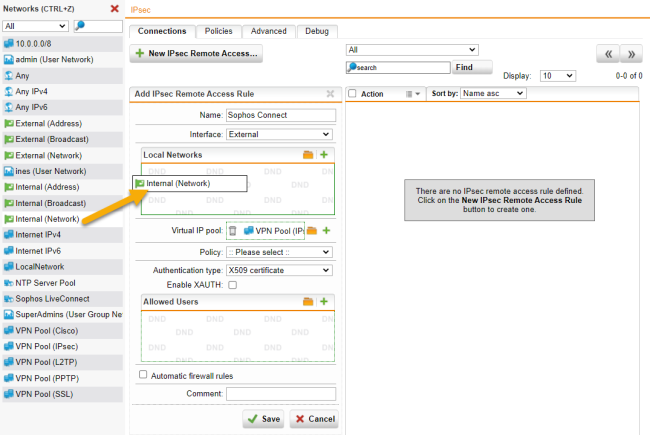
Add an IPsec rule
Create a new IPsec connection, configure basic settings, and access control.
-
Go to Remote Access > IPsec > Connections.
-
Click New IPsec Remote Access Rule.
The Add IPsec Remote Access Rule dialog box opens.
-
Specify the following settings:
Name: Enter a descriptive name for this connection.
Interface: Select the network interface to use as the local endpoint of the IPsec tunnel.
Local networks: Select the local networks that endpoint devices should be able to reach.
Note: If you want the IPsec-connected users to be able to access the internet, select Any in Local Networks. Then you must define appropriate masquerading or NAT rules later to allow this network traffic.
Virtual IP pool: By default, the UTM assigns addresses from the private IP space 10.242.4.x/24. This network is called the VPN Pool (IPsec). To use a different network, create a different network here, or change the definition of VPN Pool (IPsec) under Definitions & Users > Network Definitions.
Policy: Select a predefined policy (in this example: AES-256) or go to the IPsec > Policies tab to define your own policy.
Authentication type: IPsec remote access supports the following authentication types:
-
CA DN match: The authentication is based on the Distinguished Name (DN).
-
Authority: Select the certificate authority VPN Signing CA for the VPN users.
-
DN mask: To use a Distinguished Name as an ID, you need information from the X.509 index. Possible indications are Country (C), State (ST), Local (L), Organization (O), Unit (OU), Common Name (CN), and E-Mail Address (E).
-
Enable XAUTH (optional): Turn on to use extended authentication of users against configured backends.
-
Preshared key
-
Preshared key: Enter the shared secret. This is a secure phrase or password used to encrypt the traffic using the encryption algorithm for IPsec.
-
Confirm: Confirm the shared secret.
Security Note: Use a secure password. Ensure that this password does not fall into the hands of unauthorized third parties. With this password, an attacker can build a connection to the internal network. We recommend changing this password at regular intervals.
Enable XAUTH (optional): Turn on to use extended authentication of users against configured backends. Turn on for users to be able to retrieve their access information from the User Portal and add the users to the Allowed users box.
-
-
-
X.509 certificate
For authentication with an X.509 certificate, users can download the certificate file in addition to the Sophos Connect client from the User Portal.
-
Enable XAUTH (optional): Turn on to use extended authentication of users against configured backends.
-
Allowed users: Select the users who had been created automatically and who should use the IPsec connection.
-
Automatic firewall rules: Select to automatically create firewall rules for the tunnel traffic. These rules exist only for the lifetime of the tunnel. If you don’t select this option, you must define the firewall rules manually (see "Create the firewall and masquerading rules""Create the firewall and masquerading rules").
-
Comment (optional): Add a description or other information about the IPsec connection.
-
- Click Save.
-
Enable the IPsec rule.
You can enable the rule now or later after completing the whole UTM configuration.
Click the toggle switch in front of the rule to activate the rule.
The switch turns green. The IPsec remote access rule is active now.
Cross Reference: For more information about remote access, go to Remote Access in the UTM administration guide.
